#include <oauth2_middleware.h>
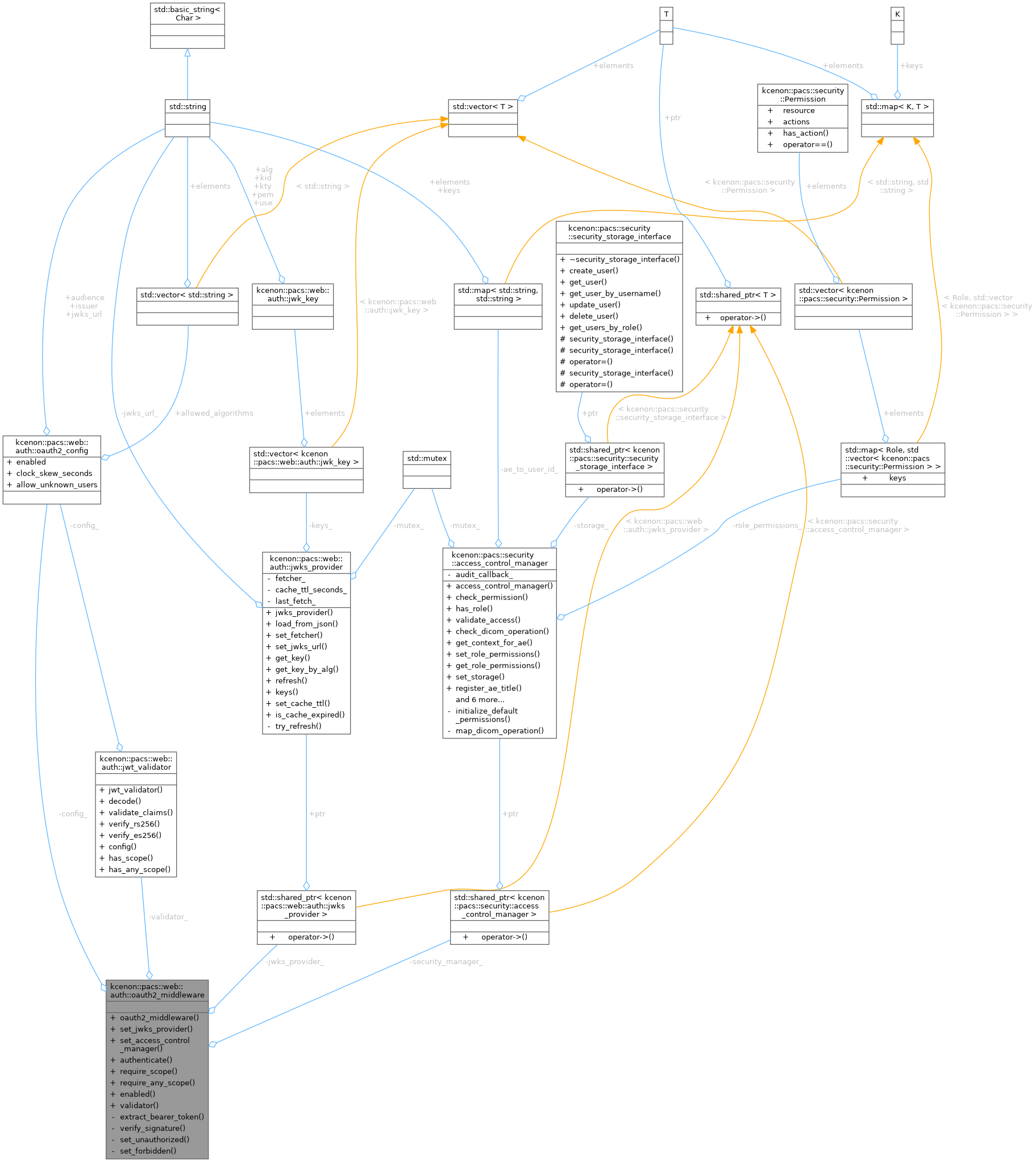
Public Member Functions | |
| oauth2_middleware (const oauth2_config &config) | |
| Construct middleware with OAuth 2.0 configuration. | |
| void | set_jwks_provider (std::shared_ptr< jwks_provider > provider) |
| Set the JWKS provider for signature verification. | |
| void | set_access_control_manager (std::shared_ptr< security::access_control_manager > manager) |
| Set the access control manager for RBAC integration. | |
| std::optional< auth_result > | authenticate (const crow::request &req, crow::response &res) const |
| Authenticate a request using OAuth 2.0 Bearer token. | |
| bool | require_scope (const jwt_claims &claims, crow::response &res, std::string_view required_scope) const |
| Check if the authenticated request has a required scope. | |
| bool | require_any_scope (const jwt_claims &claims, crow::response &res, const std::vector< std::string > &required_scopes) const |
| Check if the request has any of the required scopes. | |
| bool | enabled () const noexcept |
| Check if OAuth 2.0 is enabled. | |
| const jwt_validator & | validator () const noexcept |
| Get the underlying JWT validator. | |
Private Member Functions | |
| std::optional< std::string_view > | extract_bearer_token (const crow::request &req) const |
| Extract Bearer token from Authorization header. | |
| bool | verify_signature (const jwt_token &token) const |
| Verify token signature using JWKS keys. | |
Static Private Member Functions | |
| static void | set_unauthorized (crow::response &res, std::string_view message) |
| Set 401 Unauthorized response. | |
| static void | set_forbidden (crow::response &res, std::string_view message) |
| Set 403 Forbidden response. | |
Private Attributes | |
| oauth2_config | config_ |
| jwt_validator | validator_ |
| std::shared_ptr< jwks_provider > | jwks_provider_ |
| std::shared_ptr< security::access_control_manager > | security_manager_ |
Detailed Description
Definition at line 111 of file oauth2_middleware.h.
Constructor & Destructor Documentation
◆ oauth2_middleware()
|
explicit |
Construct middleware with OAuth 2.0 configuration.
- Parameters
-
config The OAuth 2.0 configuration
Definition at line 32 of file oauth2_middleware.cpp.
Member Function Documentation
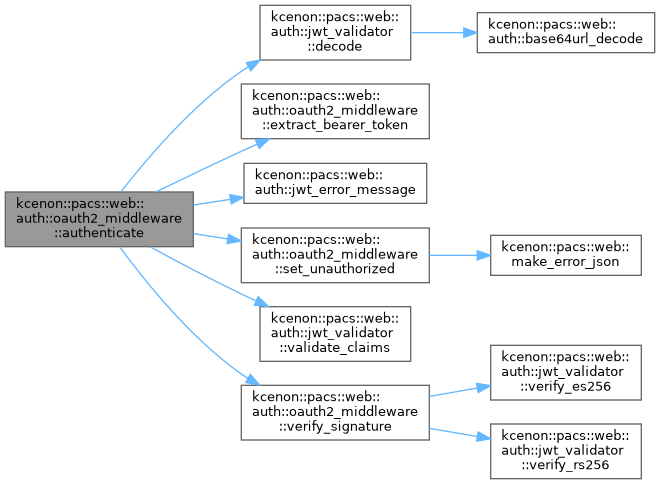
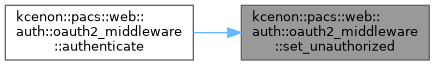
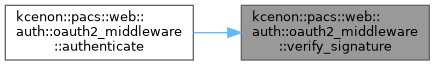
◆ authenticate()
|
nodiscard |
Authenticate a request using OAuth 2.0 Bearer token.
Extracts the Bearer token, validates JWT claims, verifies the signature, and creates an auth_result containing both the user_context and validated claims. On failure, sets an appropriate error response (401 or 403).
- Parameters
-
req The HTTP request res The HTTP response (set on error)
- Returns
- auth_result on success, std::nullopt on failure
Definition at line 45 of file oauth2_middleware.cpp.
References kcenon::pacs::web::auth::oauth2_config::allow_unknown_users, config_, kcenon::pacs::web::auth::jwt_validator::decode(), extract_bearer_token(), kcenon::pacs::security::User::id, kcenon::pacs::web::auth::jwt_error_message(), kcenon::pacs::web::auth::none, security_manager_, set_unauthorized(), kcenon::pacs::web::auth::jwt_validator::validate_claims(), validator_, verify_signature(), and kcenon::pacs::security::Viewer.
◆ enabled()
|
nodiscardnoexcept |
Check if OAuth 2.0 is enabled.
Definition at line 138 of file oauth2_middleware.cpp.
References config_, and kcenon::pacs::web::auth::oauth2_config::enabled.
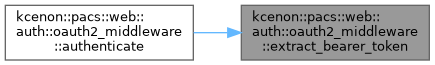
◆ extract_bearer_token()
|
nodiscardprivate |
Extract Bearer token from Authorization header.
Definition at line 150 of file oauth2_middleware.cpp.
Referenced by authenticate().
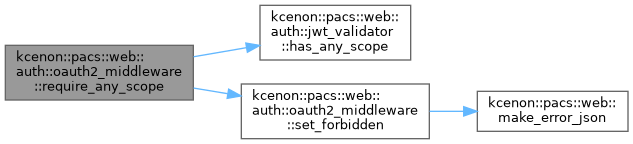
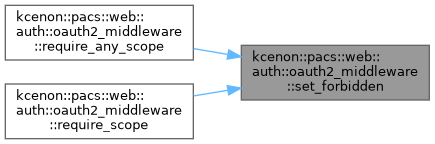
◆ require_any_scope()
|
nodiscard |
Check if the request has any of the required scopes.
- Parameters
-
claims JWT claims from a previously validated token res The HTTP response (set on failure) required_scopes List of acceptable scopes
- Returns
- true if at least one scope is present
Definition at line 121 of file oauth2_middleware.cpp.
References kcenon::pacs::web::auth::jwt_validator::has_any_scope(), and set_forbidden().
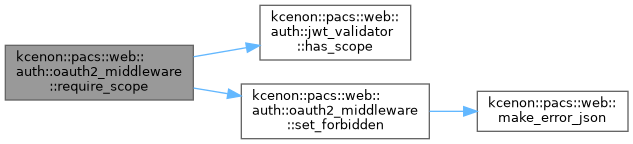
◆ require_scope()
|
nodiscard |
Check if the authenticated request has a required scope.
Must be called after authenticate(). Returns false and sets 403 response if the required scope is missing.
- Parameters
-
claims JWT claims from a previously validated token res The HTTP response (set on failure) required_scope The required OAuth scope
- Returns
- true if the scope is present
Definition at line 108 of file oauth2_middleware.cpp.
References kcenon::pacs::web::auth::jwt_validator::has_scope(), and set_forbidden().
◆ set_access_control_manager()
| void kcenon::pacs::web::auth::oauth2_middleware::set_access_control_manager | ( | std::shared_ptr< security::access_control_manager > | manager | ) |
Set the access control manager for RBAC integration.
- Parameters
-
manager Shared pointer to access control manager
Definition at line 40 of file oauth2_middleware.cpp.
References security_manager_.
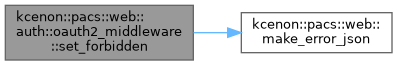
◆ set_forbidden()
|
staticprivate |
Set 403 Forbidden response.
Definition at line 207 of file oauth2_middleware.cpp.
References kcenon::pacs::web::make_error_json().
Referenced by require_any_scope(), and require_scope().
◆ set_jwks_provider()
| void kcenon::pacs::web::auth::oauth2_middleware::set_jwks_provider | ( | std::shared_ptr< jwks_provider > | provider | ) |
Set the JWKS provider for signature verification.
- Parameters
-
provider Shared pointer to JWKS provider
Definition at line 35 of file oauth2_middleware.cpp.
References jwks_provider_.
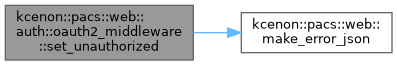
◆ set_unauthorized()
|
staticprivate |
Set 401 Unauthorized response.
Definition at line 199 of file oauth2_middleware.cpp.
References kcenon::pacs::web::make_error_json().
Referenced by authenticate().
◆ validator()
|
nodiscardnoexcept |
Get the underlying JWT validator.
Definition at line 142 of file oauth2_middleware.cpp.
References validator_.
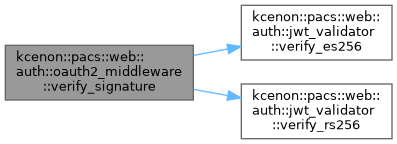
◆ verify_signature()
|
nodiscardprivate |
Verify token signature using JWKS keys.
Definition at line 173 of file oauth2_middleware.cpp.
References kcenon::pacs::web::auth::jwt_header::alg, kcenon::pacs::web::auth::jwt_token::header, jwks_provider_, kcenon::pacs::web::auth::jwt_header::kid, validator_, kcenon::pacs::web::auth::jwt_validator::verify_es256(), and kcenon::pacs::web::auth::jwt_validator::verify_rs256().
Referenced by authenticate().
Member Data Documentation
◆ config_
|
private |
Definition at line 187 of file oauth2_middleware.h.
Referenced by authenticate(), and enabled().
◆ jwks_provider_
|
private |
Definition at line 189 of file oauth2_middleware.h.
Referenced by set_jwks_provider(), and verify_signature().
◆ security_manager_
|
private |
Definition at line 190 of file oauth2_middleware.h.
Referenced by authenticate(), and set_access_control_manager().
◆ validator_
|
private |
Definition at line 188 of file oauth2_middleware.h.
Referenced by authenticate(), validator(), and verify_signature().
The documentation for this class was generated from the following files:
- include/kcenon/pacs/web/auth/oauth2_middleware.h
- src/web/auth/oauth2_middleware.cpp