Namespaces | |
| namespace | Action |
| specific actions that can be performed | |
| namespace | atna_event_ids |
| namespace | atna_event_types |
| namespace | atna_object_id_types |
| namespace | atna_role_ids |
| namespace | hipaa_identifiers |
| HIPAA Safe Harbor identifiers (18 categories) | |
Classes | |
| class | access_control_manager |
| Manages permissions and access checks. More... | |
| struct | AccessCheckResult |
| Result of an access check. More... | |
| struct | anonymization_report |
| Report generated after anonymization. More... | |
| class | anonymizer |
| struct | atna_active_participant |
| An active participant in the audit event. More... | |
| class | atna_audit_logger |
| RFC 3881 XML audit message generator. More... | |
| struct | atna_audit_message |
| Complete RFC 3881 audit message. More... | |
| struct | atna_audit_source |
| Identifies the audit source system. More... | |
| struct | atna_coded_value |
| A coded value with code, code system name, and display name. More... | |
| struct | atna_config |
| Configuration for ATNA audit logging. More... | |
| struct | atna_config_validation |
| Validation result for ATNA configuration. More... | |
| struct | atna_object_detail |
| Additional detail about a participant object. More... | |
| struct | atna_participant_object |
| An object (patient, study, query) involved in the event. More... | |
| class | atna_service_auditor |
| High-level facade for emitting ATNA audit events from DICOM services. More... | |
| class | atna_syslog_transport |
| Sends ATNA audit messages via Syslog protocol. More... | |
| class | certificate |
| class | certificate_chain |
| Represents a certificate chain for validation. More... | |
| struct | certificate_constraints |
| Certificate validation constraints. More... | |
| class | certificate_impl |
| struct | cipher_suite_spec |
| TLS cipher suite specification. More... | |
| class | digital_signature |
| struct | Permission |
| Represents a permission grant. More... | |
| class | private_key |
| class | private_key_impl |
| class | security_storage_interface |
| Abstract interface for persisting security data (Users, Roles) More... | |
| struct | signature_info |
| Information about a digital signature. More... | |
| struct | syslog_transport_config |
| Configuration for the Syslog transport. More... | |
| struct | tag_action_config |
| Configuration for a custom tag action. More... | |
| struct | tag_action_record |
| Record of an action performed on a tag. More... | |
| class | tls_policy |
| TLS security policy configuration. More... | |
| class | uid_mapping |
| struct | User |
| Represents a user in the system. More... | |
| class | user_context |
| Represents the security context for a user session. More... | |
Typedefs | |
| using | AccessAuditCallback |
| Callback for audit logging of access attempts. | |
Enumerations | |
| enum class | DicomOperation { CStore , CFind , CMove , CGet , CEcho , NCreate , NSet , NGet , NDelete , NAction , NEventReport } |
| DICOM operation types for permission checking. More... | |
| enum class | anonymization_profile : std::uint8_t { basic = 0 , clean_pixel = 1 , clean_descriptions = 2 , retain_longitudinal = 3 , retain_patient_characteristics = 4 , hipaa_safe_harbor = 5 , gdpr_compliant = 6 } |
| DICOM de-identification profiles based on PS3.15 Annex E. More... | |
| enum class | private_tag_action : std::uint8_t { keep , remove_all , remove_data } |
| Action to take on private tags during anonymization. More... | |
| enum class | atna_event_action : char { create = 'C' , read = 'R' , update = 'U' , delete_action = 'D' , execute = 'E' } |
| Action that triggered the audit event. More... | |
| enum class | atna_event_outcome : uint8_t { success = 0 , minor_failure = 4 , serious_failure = 8 , major_failure = 12 } |
| Outcome of the audited event. More... | |
| enum class | atna_network_access_type : uint8_t { machine_name = 1 , ip_address = 2 , phone_number = 3 } |
| Type of network access point identifier. More... | |
| enum class | atna_object_type : uint8_t { person = 1 , system_object = 2 , organization = 3 , other = 4 } |
| Type of participant object. More... | |
| enum class | atna_object_role : uint8_t { patient = 1 , location = 2 , report = 3 , resource = 4 , master_file = 5 , user = 6 , list = 7 , doctor = 8 , subscriber = 9 , guarantor = 10 , security_user_entity = 11 , security_user_group = 12 , security_resource = 13 , security_granularity_def = 14 , provider = 15 , data_destination = 16 , data_repository = 17 , schedule = 18 , customer = 19 , job = 20 , job_stream = 21 , table = 22 , routing_criteria = 23 , query = 24 } |
| Role of the participant object in the event. More... | |
| enum class | syslog_facility : uint8_t { kern = 0 , user = 1 , mail = 2 , daemon = 3 , auth = 4 , syslog = 5 , lpr = 6 , news = 7 , uucp = 8 , cron = 9 , authpriv = 10 , ftp = 11 , ntp = 12 , log_audit = 13 , log_alert = 14 , clock = 15 , local0 = 16 , local1 = 17 , local2 = 18 , local3 = 19 , local4 = 20 , local5 = 21 , local6 = 22 , local7 = 23 } |
| Syslog facility values. More... | |
| enum class | syslog_severity : uint8_t { emergency = 0 , alert = 1 , critical = 2 , error = 3 , warning = 4 , notice = 5 , informational = 6 , debug = 7 } |
| Syslog severity levels. More... | |
| enum class | syslog_transport_protocol : uint8_t { udp , tls } |
| Syslog transport protocol. More... | |
| enum class | ResourceType { Study , Metadata , System , Audit , User , Role , Series , Image } |
| Categories of resources requiring protection. More... | |
| enum class | Role { Viewer , Technologist , Radiologist , Administrator , System } |
| User roles in the PACS system. More... | |
| enum class | signature_algorithm { rsa_sha256 , rsa_sha384 , rsa_sha512 , ecdsa_sha256 , ecdsa_sha384 } |
| Signature algorithms supported for DICOM digital signatures. More... | |
| enum class | signature_status { valid , invalid , expired , untrusted_signer , revoked , no_signature } |
| Status of signature verification. More... | |
| enum class | mac_algorithm { sha256 , sha384 , sha512 } |
| MAC algorithm identifiers per DICOM PS3.15. More... | |
| enum class | certificate_type { x509_certificate , x509_certificate_chain } |
| Certificate type for DICOM signatures. More... | |
| enum class | tag_action : std::uint8_t { remove = 0 , empty = 1 , remove_or_empty = 2 , keep = 3 , replace = 4 , replace_uid = 5 , hash = 6 , encrypt = 7 , shift_date = 8 } |
| Actions to perform on DICOM attributes during de-identification. More... | |
| enum class | tls_profile { bcp195_basic , bcp195_non_downgrading , bcp195_extended } |
| TLS policy profile levels. More... | |
Functions | |
| constexpr auto | to_string (anonymization_profile profile) noexcept -> std::string_view |
| Convert profile enum to string representation. | |
| auto | profile_from_string (std::string_view name) -> std::optional< anonymization_profile > |
| Parse profile from string. | |
| atna_config | make_default_atna_config () |
| Create a default ATNA configuration. | |
| std::string | to_json (const atna_config &config) |
| Serialize an atna_config to a JSON string. | |
| atna_config | parse_atna_config (std::string_view json_str) |
| Parse an atna_config from a JSON string. | |
| atna_config_validation | validate (const atna_config &config) |
| Validate an ATNA configuration. | |
| constexpr std::string_view | to_string (Role role) |
| Convert Role to string. | |
| std::optional< Role > | parse_role (std::string_view str) |
| Parse Role from string. | |
| constexpr std::string_view | to_string (signature_algorithm algo) |
| Convert signature_algorithm to string representation. | |
| std::optional< signature_algorithm > | parse_signature_algorithm (std::string_view str) |
| Parse signature_algorithm from string. | |
| constexpr std::string_view | to_string (signature_status status) |
| Convert signature_status to string representation. | |
| constexpr std::string_view | to_dicom_uid (mac_algorithm algo) |
| Convert mac_algorithm to DICOM UID string. | |
| constexpr std::string_view | to_dicom_term (certificate_type type) |
| Convert certificate_type to DICOM defined term. | |
| constexpr auto | to_string (tag_action action) noexcept -> std::string_view |
| Convert tag action enum to string representation. | |
| std::string_view | to_string (tls_profile profile) noexcept |
| Convert TLS profile to string. | |
| std::optional< tls_profile > | parse_tls_profile (std::string_view str) noexcept |
| Parse TLS profile from string. | |
| std::vector< tls_profile > | available_tls_profiles () |
| Get a list of all available TLS profiles. | |
| X509 * | get_x509_from_certificate (const certificate &cert) |
Typedef Documentation
◆ AccessAuditCallback
Callback for audit logging of access attempts.
Definition at line 64 of file access_control_manager.h.
Enumeration Type Documentation
◆ anonymization_profile
|
strong |
DICOM de-identification profiles based on PS3.15 Annex E.
Each profile defines a set of actions to be performed on specific DICOM attributes to achieve varying levels of de-identification.
Profile selection depends on:
- Regulatory requirements (HIPAA, GDPR)
- Use case (research, clinical trial, data sharing)
- Need to preserve clinical utility
- See also
- DICOM PS3.15 Annex E Table E.1-1
Definition at line 40 of file anonymization_profile.h.
◆ atna_event_action
|
strong |
Action that triggered the audit event.
| Enumerator | |
|---|---|
| create | |
| read | |
| update | |
| delete_action | |
| execute | |
Definition at line 53 of file atna_audit_logger.h.
◆ atna_event_outcome
|
strong |
Outcome of the audited event.
| Enumerator | |
|---|---|
| success | |
| minor_failure | |
| serious_failure | |
| major_failure | |
Definition at line 68 of file atna_audit_logger.h.
◆ atna_network_access_type
|
strong |
Type of network access point identifier.
| Enumerator | |
|---|---|
| machine_name | |
| ip_address | |
| phone_number | |
Definition at line 82 of file atna_audit_logger.h.
◆ atna_object_role
|
strong |
Role of the participant object in the event.
Definition at line 105 of file atna_audit_logger.h.
◆ atna_object_type
|
strong |
Type of participant object.
| Enumerator | |
|---|---|
| person | |
| system_object | |
| organization | |
| other | |
Definition at line 95 of file atna_audit_logger.h.
◆ certificate_type
|
strong |
Certificate type for DICOM signatures.
Specifies the type of certificate used in the signature.
| Enumerator | |
|---|---|
| x509_certificate | X.509 certificate (most common) |
| x509_certificate_chain | Full X.509 certificate chain. |
Definition at line 155 of file signature_types.h.
◆ DicomOperation
|
strong |
DICOM operation types for permission checking.
Definition at line 32 of file access_control_manager.h.
◆ mac_algorithm
|
strong |
MAC algorithm identifiers per DICOM PS3.15.
These identifiers are used in the MAC Algorithm (0400,0015) attribute.
| Enumerator | |
|---|---|
| sha256 | SHA-256 (recommended) |
| sha384 | SHA-384. |
| sha512 | SHA-512. |
Definition at line 130 of file signature_types.h.
◆ private_tag_action
|
strong |
Action to take on private tags during anonymization.
DICOM PS3.15 Annex E recommends removing private data elements during de-identification, as they may contain Protected Health Information (PHI) in vendor-specific formats.
- See also
- DICOM PS3.15 Annex E - Basic Profile
Definition at line 49 of file anonymizer.h.
◆ ResourceType
|
strong |
Categories of resources requiring protection.
| Enumerator | |
|---|---|
| Study | DICOM studies/series/instances. |
| Metadata | Patient/Study metadata. |
| System | System configuration and services. |
| Audit | Audit logs. |
| User | User management. |
| Role | Role management. |
| Series | DICOM Series. |
| Image | DICOM Image. |
Definition at line 25 of file permission.h.
◆ Role
|
strong |
User roles in the PACS system.
| Enumerator | |
|---|---|
| Viewer | Read-only access to studies. |
| Technologist | Can upload/modify studies, but not delete. |
| Radiologist | Full clinical access (includes verification) |
| Administrator | User management, system config. |
| System | Internal system operations. |
◆ signature_algorithm
|
strong |
Signature algorithms supported for DICOM digital signatures.
Per DICOM PS3.15, the following algorithms are defined:
- RSA with SHA-256 (recommended)
- RSA with SHA-384
- RSA with SHA-512
- ECDSA with SHA-256 (for smaller key sizes)
- ECDSA with SHA-384
Definition at line 40 of file signature_types.h.
◆ signature_status
|
strong |
Status of signature verification.
Definition at line 81 of file signature_types.h.
◆ syslog_facility
|
strong |
Syslog facility values.
The audit facility is typically 10 (security/authorization) or 13 (log audit) per IHE ATNA recommendations.
Definition at line 38 of file atna_syslog_transport.h.
◆ syslog_severity
|
strong |
Syslog severity levels.
| Enumerator | |
|---|---|
| emergency | |
| alert | |
| critical | |
| error | |
| warning | |
| notice | |
| informational | Default for audit events. |
| debug | |
Definition at line 72 of file atna_syslog_transport.h.
◆ syslog_transport_protocol
|
strong |
Syslog transport protocol.
| Enumerator | |
|---|---|
| udp | UDP (RFC 5426) — Fire-and-forget. |
| tls | TLS over TCP (RFC 5425) — Secure. |
Definition at line 90 of file atna_syslog_transport.h.
◆ tag_action
|
strong |
Actions to perform on DICOM attributes during de-identification.
These actions correspond to the action codes defined in DICOM PS3.15 Annex E Table E.1-1.
Definition at line 39 of file tag_action.h.
◆ tls_profile
|
strong |
TLS policy profile levels.
Predefined security profiles aligned with DICOM PS3.15 and BCP 195.
Definition at line 36 of file tls_policy.h.
Function Documentation
◆ available_tls_profiles()
|
nodiscard |
Get a list of all available TLS profiles.
Definition at line 152 of file tls_policy.cpp.
References bcp195_basic, bcp195_extended, and bcp195_non_downgrading.
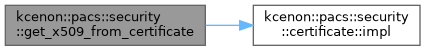
◆ get_x509_from_certificate()
| X509 * kcenon::pacs::security::get_x509_from_certificate | ( | const certificate & | cert | ) |
Definition at line 276 of file digital_signature.cpp.
References kcenon::pacs::security::certificate::impl().
◆ make_default_atna_config()
|
nodiscard |
Create a default ATNA configuration.
Returns a configuration with sensible defaults:
- Disabled by default (must be explicitly enabled)
- UDP transport to localhost:514
- All event types enabled
- Returns
- Default atna_config
Definition at line 156 of file atna_config.cpp.
◆ parse_atna_config()
|
nodiscard |
Parse an atna_config from a JSON string.
Reads a JSON configuration string and populates an atna_config struct. Fields not present in the JSON retain their default values.
- Parameters
-
json_str JSON string to parse
- Returns
- Parsed atna_config, or defaults for malformed input
Definition at line 196 of file atna_config.cpp.
References kcenon::pacs::security::syslog_transport_config::app_name, kcenon::pacs::security::atna_config::audit_authentication, kcenon::pacs::security::atna_config::audit_query, kcenon::pacs::security::atna_config::audit_security_alerts, kcenon::pacs::security::atna_config::audit_source_id, kcenon::pacs::security::atna_config::audit_storage, kcenon::pacs::security::syslog_transport_config::ca_cert_path, kcenon::pacs::security::syslog_transport_config::client_cert_path, kcenon::pacs::security::syslog_transport_config::client_key_path, kcenon::pacs::security::atna_config::enabled, kcenon::pacs::security::syslog_transport_config::host, kcenon::pacs::security::syslog_transport_config::port, kcenon::pacs::security::syslog_transport_config::protocol, kcenon::pacs::security::atna_config::transport, and kcenon::pacs::security::syslog_transport_config::verify_server.
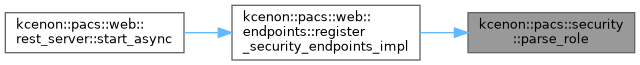
◆ parse_role()
|
inline |
Parse Role from string.
Definition at line 50 of file role.h.
References Administrator, Radiologist, System, Technologist, and Viewer.
Referenced by kcenon::pacs::web::endpoints::register_security_endpoints_impl().
◆ parse_signature_algorithm()
|
inline |
Parse signature_algorithm from string.
- Parameters
-
str The string to parse
- Returns
- Optional containing the algorithm, or nullopt if parsing fails
Definition at line 69 of file signature_types.h.
References ecdsa_sha256, ecdsa_sha384, rsa_sha256, rsa_sha384, and rsa_sha512.
◆ parse_tls_profile()
|
nodiscardnoexcept |
Parse TLS profile from string.
Definition at line 25 of file tls_policy.cpp.
References bcp195_basic, bcp195_extended, and bcp195_non_downgrading.
◆ profile_from_string()
|
inlinenodiscard |
Parse profile from string.
- Parameters
-
name String name of the profile
- Returns
- Optional containing the profile, or nullopt if invalid
- Examples
- dcm_anonymize/main.cpp.
Definition at line 158 of file anonymization_profile.h.
References basic, clean_descriptions, clean_pixel, gdpr_compliant, hipaa_safe_harbor, name, retain_longitudinal, and retain_patient_characteristics.
◆ to_dicom_term()
|
constexpr |
Convert certificate_type to DICOM defined term.
- Parameters
-
type The certificate type
- Returns
- DICOM defined term
Definition at line 165 of file signature_types.h.
References x509_certificate, and x509_certificate_chain.
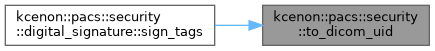
◆ to_dicom_uid()
|
constexpr |
Convert mac_algorithm to DICOM UID string.
- Parameters
-
algo The MAC algorithm
- Returns
- DICOM defined term for the algorithm
Definition at line 141 of file signature_types.h.
References sha256, sha384, and sha512.
Referenced by kcenon::pacs::security::digital_signature::sign_tags().
◆ to_json()
|
nodiscard |
Serialize an atna_config to a JSON string.
Produces a compact JSON representation suitable for configuration files and REST API responses.
- Parameters
-
config The configuration to serialize
- Returns
- JSON string
Definition at line 164 of file atna_config.cpp.
References kcenon::pacs::security::syslog_transport_config::app_name, kcenon::pacs::security::atna_config::audit_authentication, kcenon::pacs::security::atna_config::audit_query, kcenon::pacs::security::atna_config::audit_security_alerts, kcenon::pacs::security::atna_config::audit_source_id, kcenon::pacs::security::atna_config::audit_storage, kcenon::pacs::security::syslog_transport_config::ca_cert_path, kcenon::pacs::security::syslog_transport_config::client_cert_path, kcenon::pacs::security::syslog_transport_config::client_key_path, kcenon::pacs::security::atna_config::enabled, kcenon::pacs::security::syslog_transport_config::host, kcenon::pacs::security::syslog_transport_config::port, kcenon::pacs::security::syslog_transport_config::protocol, kcenon::pacs::security::atna_config::transport, and kcenon::pacs::security::syslog_transport_config::verify_server.
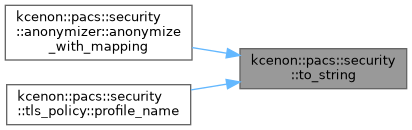
◆ to_string() [1/6]
|
nodiscardconstexprnoexcept |
Convert profile enum to string representation.
- Parameters
-
profile The anonymization profile
- Returns
- String name of the profile
Definition at line 132 of file anonymization_profile.h.
References basic, clean_descriptions, clean_pixel, gdpr_compliant, hipaa_safe_harbor, retain_longitudinal, and retain_patient_characteristics.
Referenced by kcenon::pacs::security::anonymizer::anonymize_with_mapping(), and kcenon::pacs::security::tls_policy::profile_name().
◆ to_string() [2/6]
|
constexpr |
Convert Role to string.
Definition at line 36 of file role.h.
References Administrator, Radiologist, System, Technologist, and Viewer.
◆ to_string() [3/6]
|
constexpr |
Convert signature_algorithm to string representation.
- Parameters
-
algo The algorithm to convert
- Returns
- String representation of the algorithm
Definition at line 53 of file signature_types.h.
References ecdsa_sha256, ecdsa_sha384, rsa_sha256, rsa_sha384, and rsa_sha512.
◆ to_string() [4/6]
|
constexpr |
Convert signature_status to string representation.
- Parameters
-
status The status to convert
- Returns
- String representation of the status
Definition at line 95 of file signature_types.h.
References expired, invalid, no_signature, revoked, untrusted_signer, and valid.
◆ to_string() [5/6]
|
nodiscardconstexprnoexcept |
Convert tag action enum to string representation.
- Parameters
-
action The tag action
- Returns
- String name of the action
Definition at line 117 of file tag_action.h.
References empty, encrypt, hash, keep, remove, remove_or_empty, replace, replace_uid, and shift_date.
◆ to_string() [6/6]
|
nodiscardnoexcept |
Convert TLS profile to string.
Definition at line 13 of file tls_policy.cpp.
References bcp195_basic, bcp195_extended, and bcp195_non_downgrading.
◆ validate()
|
nodiscard |
Validate an ATNA configuration.
Checks for:
- Non-empty audit_source_id
- Non-empty transport host
- Valid port range (1-65535)
- TLS certificate paths exist when protocol is TLS
- Parameters
-
config The configuration to validate
- Returns
- Validation result with any errors
Definition at line 283 of file atna_config.cpp.
References kcenon::pacs::security::atna_config::audit_source_id, kcenon::pacs::security::syslog_transport_config::ca_cert_path, kcenon::pacs::security::syslog_transport_config::client_cert_path, kcenon::pacs::security::syslog_transport_config::client_key_path, kcenon::pacs::security::atna_config_validation::errors, kcenon::pacs::security::syslog_transport_config::host, kcenon::pacs::security::syslog_transport_config::port, kcenon::pacs::security::syslog_transport_config::protocol, tls, kcenon::pacs::security::atna_config::transport, and kcenon::pacs::security::atna_config_validation::valid.