#include <jwt_validator.h>
Public Member Functions | |
| jwt_validator (const oauth2_config &config) | |
| Construct validator with OAuth 2.0 configuration. | |
| std::pair< jwt_token, jwt_error > | decode (std::string_view token_string) const |
| Decode a JWT token string into its components. | |
| jwt_error | validate_claims (const jwt_claims &claims) const |
| Validate JWT claims against configuration. | |
| bool | verify_rs256 (const jwt_token &token, std::string_view public_key_pem) const |
| Verify RS256 (RSA-SHA256) signature. | |
| bool | verify_es256 (const jwt_token &token, std::string_view public_key_pem) const |
| Verify ES256 (ECDSA-SHA256) signature. | |
| const oauth2_config & | config () const noexcept |
| Get the OAuth 2.0 configuration. | |
Static Public Member Functions | |
| static bool | has_scope (const jwt_claims &claims, std::string_view scope) noexcept |
| Check if token has a specific scope. | |
| static bool | has_any_scope (const jwt_claims &claims, const std::vector< std::string > &scopes) noexcept |
| Check if token has any of the specified scopes. | |
Private Attributes | |
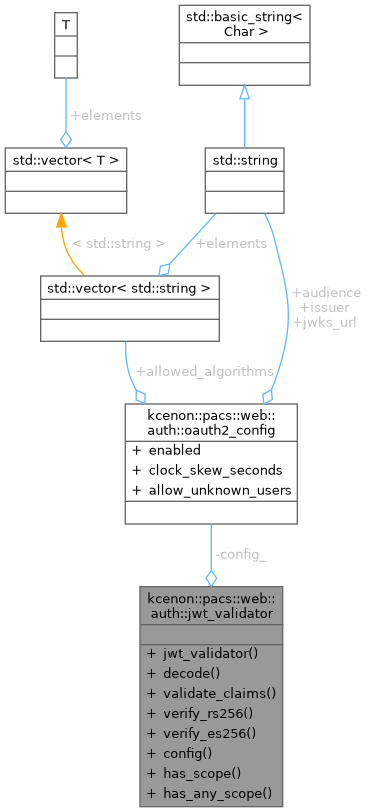
| oauth2_config | config_ |
Detailed Description
Definition at line 124 of file jwt_validator.h.
Constructor & Destructor Documentation
◆ jwt_validator()
|
explicit |
Construct validator with OAuth 2.0 configuration.
- Parameters
-
config The OAuth 2.0 configuration
Definition at line 178 of file jwt_validator.cpp.
Member Function Documentation
◆ config()
|
nodiscardnoexcept |
Get the OAuth 2.0 configuration.
Definition at line 481 of file jwt_validator.cpp.
References config_.
◆ decode()
|
nodiscard |
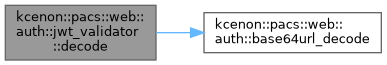
Decode a JWT token string into its components.
Splits the token, decodes Base64url segments, and parses JSON. Does NOT verify the signature.
- Parameters
-
token_string The raw JWT string (header.payload.signature)
- Returns
- Pair of decoded token and error code
Definition at line 181 of file jwt_validator.cpp.
References kcenon::pacs::web::auth::jwt_header::alg, kcenon::pacs::web::auth::oauth2_config::allowed_algorithms, kcenon::pacs::web::auth::jwt_claims::aud, kcenon::pacs::web::auth::base64url_decode(), kcenon::pacs::web::auth::jwt_token::claims, config_, kcenon::pacs::web::auth::jwt_claims::exp, kcenon::pacs::web::auth::jwt_token::header, kcenon::pacs::web::auth::jwt_token::header_payload, kcenon::pacs::web::auth::jwt_claims::iat, kcenon::pacs::web::auth::invalid_base64, kcenon::pacs::web::auth::invalid_json, kcenon::pacs::web::auth::jwt_claims::iss, kcenon::pacs::web::auth::jwt_claims::jti, kcenon::pacs::web::auth::jwt_header::kid, kcenon::pacs::web::auth::malformed_token, kcenon::pacs::web::auth::missing_required_claim, kcenon::pacs::web::auth::jwt_claims::nbf, kcenon::pacs::web::auth::none, kcenon::pacs::web::auth::jwt_claims::scopes, kcenon::pacs::web::auth::jwt_token::signature_bytes, kcenon::pacs::web::auth::jwt_claims::sub, kcenon::pacs::web::auth::jwt_header::typ, and kcenon::pacs::web::auth::unsupported_algorithm.
Referenced by kcenon::pacs::web::auth::oauth2_middleware::authenticate().

◆ has_any_scope()
|
staticnodiscardnoexcept |
Check if token has any of the specified scopes.
- Parameters
-
claims The token claims scopes List of acceptable scopes
- Returns
- true if at least one scope matches
Definition at line 471 of file jwt_validator.cpp.
Referenced by kcenon::pacs::web::auth::oauth2_middleware::require_any_scope().

◆ has_scope()
|
staticnodiscardnoexcept |
Check if token has a specific scope.
- Parameters
-
claims The token claims scope The required scope
- Returns
- true if the scope is present
Definition at line 463 of file jwt_validator.cpp.
Referenced by kcenon::pacs::web::auth::oauth2_middleware::require_scope().

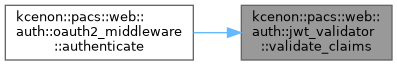
◆ validate_claims()
|
nodiscard |
Validate JWT claims against configuration.
Checks issuer, audience, expiration, and not-before claims.
- Parameters
-
claims The decoded claims to validate
- Returns
- jwt_error::none if all claims are valid
Definition at line 283 of file jwt_validator.cpp.
References kcenon::pacs::web::auth::jwt_claims::aud, kcenon::pacs::web::auth::oauth2_config::audience, kcenon::pacs::web::auth::oauth2_config::clock_skew_seconds, config_, kcenon::pacs::web::auth::jwt_claims::exp, kcenon::pacs::web::auth::invalid_audience, kcenon::pacs::web::auth::invalid_issuer, kcenon::pacs::web::auth::jwt_claims::iss, kcenon::pacs::web::auth::oauth2_config::issuer, kcenon::pacs::web::auth::missing_required_claim, kcenon::pacs::web::auth::jwt_claims::nbf, kcenon::pacs::web::auth::none, kcenon::pacs::web::auth::jwt_claims::sub, kcenon::pacs::web::auth::token_expired, and kcenon::pacs::web::auth::token_not_yet_valid.
Referenced by kcenon::pacs::web::auth::oauth2_middleware::authenticate().
◆ verify_es256()
|
nodiscard |
Verify ES256 (ECDSA-SHA256) signature.
- Parameters
-
token The decoded token with signature data public_key_pem EC public key in PEM format
- Returns
- true if signature is valid
Definition at line 451 of file jwt_validator.cpp.
Referenced by kcenon::pacs::web::auth::oauth2_middleware::verify_signature().

◆ verify_rs256()
|
nodiscard |
Verify RS256 (RSA-SHA256) signature.
- Parameters
-
token The decoded token with signature data public_key_pem RSA public key in PEM format
- Returns
- true if signature is valid
Definition at line 445 of file jwt_validator.cpp.
Referenced by kcenon::pacs::web::auth::oauth2_middleware::verify_signature().

Member Data Documentation
◆ config_
|
private |
Definition at line 201 of file jwt_validator.h.
Referenced by config(), decode(), and validate_claims().
The documentation for this class was generated from the following files:
- include/kcenon/pacs/web/auth/jwt_validator.h
- src/web/auth/jwt_validator.cpp