Manages permissions and access checks. More...
#include <access_control_manager.h>
Public Member Functions | |
| access_control_manager () | |
| bool | check_permission (const User &user, ResourceType resource, std::uint32_t action_mask) const |
| bool | has_role (const User &user, Role role) const |
| auto | validate_access (const user_context &ctx, ResourceType resource, std::uint32_t action_mask) -> kcenon::common::VoidResult |
| Validate access for a user context. | |
| AccessCheckResult | check_dicom_operation (const user_context &ctx, DicomOperation op) const |
| Check if a DICOM operation is allowed. | |
| std::optional< user_context > | get_context_for_ae (std::string_view ae_title, const std::string &session_id) const |
| Get user context for an AE Title. | |
| void | set_role_permissions (Role role, std::vector< Permission > permissions) |
| const std::vector< Permission > & | get_role_permissions (Role role) const |
| void | set_storage (std::shared_ptr< security_storage_interface > storage) |
| void | register_ae_title (std::string_view ae_title, std::string_view user_id) |
| void | unregister_ae_title (std::string_view ae_title) |
| void | set_audit_callback (AccessAuditCallback callback) |
| auto | create_user (const User &user) -> kcenon::common::VoidResult |
| auto | assign_role (std::string_view user_id, Role role) -> kcenon::common::VoidResult |
| auto | get_user (std::string_view id) -> kcenon::common::Result< User > |
| auto | get_user_by_ae_title (std::string_view ae_title) -> std::optional< User > |
| Get user by AE Title. | |
Private Member Functions | |
| void | initialize_default_permissions () |
Static Private Member Functions | |
| static std::pair< ResourceType, std::uint32_t > | map_dicom_operation (DicomOperation op) |
| Map DICOM operation to resource type and action. | |
Private Attributes | |
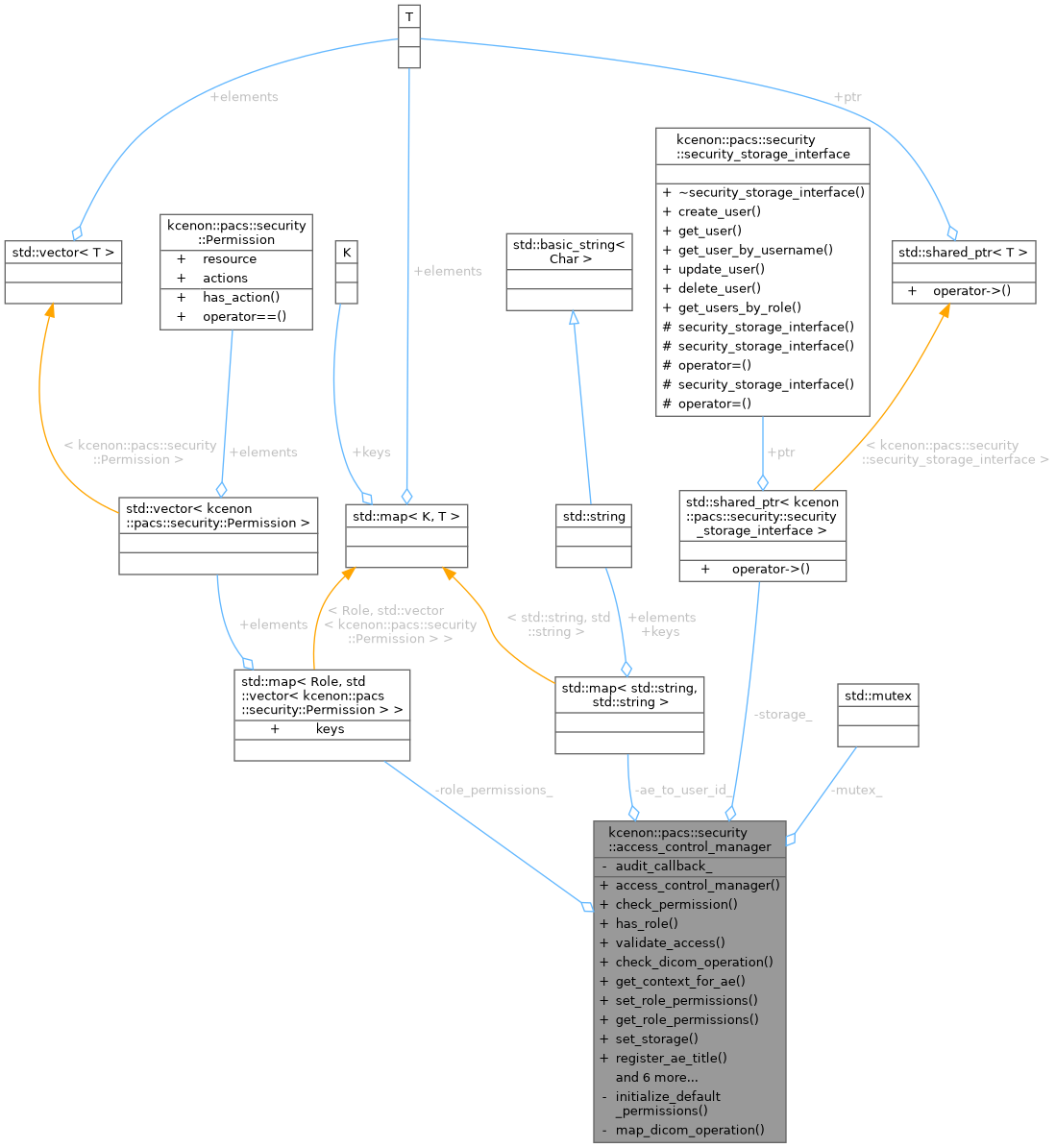
| std::map< Role, std::vector< Permission > > | role_permissions_ |
| std::shared_ptr< security_storage_interface > | storage_ |
| std::map< std::string, std::string > | ae_to_user_id_ |
| AccessAuditCallback | audit_callback_ |
| std::mutex | mutex_ |
Detailed Description
Manages permissions and access checks.
Definition at line 71 of file access_control_manager.h.
Constructor & Destructor Documentation
◆ access_control_manager()
| kcenon::pacs::security::access_control_manager::access_control_manager | ( | ) |
Definition at line 16 of file access_control_manager.cpp.
References initialize_default_permissions().
Member Function Documentation
◆ assign_role()
|
nodiscard |
Definition at line 108 of file access_control_manager.cpp.
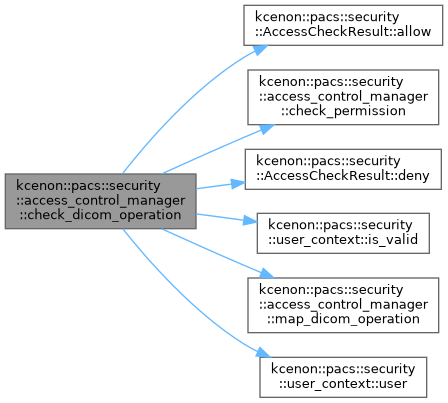
◆ check_dicom_operation()
|
nodiscard |
Check if a DICOM operation is allowed.
- Parameters
-
ctx User context op DICOM operation to check
- Returns
- AccessCheckResult with allowed status and reason
Definition at line 188 of file access_control_manager.cpp.
References kcenon::pacs::security::AccessCheckResult::allow(), audit_callback_, check_permission(), kcenon::pacs::security::AccessCheckResult::deny(), kcenon::pacs::security::user_context::is_valid(), map_dicom_operation(), kcenon::pacs::security::resource, and kcenon::pacs::security::user_context::user().
◆ check_permission()
|
nodiscard |
Definition at line 128 of file access_control_manager.cpp.
References kcenon::pacs::security::resource, and role_permissions_.
Referenced by check_dicom_operation().
◆ create_user()
|
nodiscard |
Definition at line 92 of file access_control_manager.cpp.
◆ get_context_for_ae()
|
nodiscard |
Get user context for an AE Title.
- Parameters
-
ae_title The AE Title to look up session_id Session identifier for the context
- Returns
- User context if found, std::nullopt for unregistered AE titles
Definition at line 212 of file access_control_manager.cpp.
References ae_to_user_id_, mutex_, and storage_.
◆ get_role_permissions()
|
nodiscard |
Definition at line 157 of file access_control_manager.cpp.
References kcenon::pacs::security::empty, and role_permissions_.
◆ get_user()
|
nodiscard |
Definition at line 100 of file access_control_manager.cpp.
◆ get_user_by_ae_title()
|
nodiscard |
Get user by AE Title.
- Parameters
-
ae_title The AE Title to look up
- Returns
- User if found
Definition at line 253 of file access_control_manager.cpp.
◆ has_role()
|
nodiscard |
Definition at line 147 of file access_control_manager.cpp.
◆ initialize_default_permissions()
|
private |
Definition at line 53 of file access_control_manager.cpp.
References kcenon::pacs::security::Administrator, kcenon::pacs::security::Audit, kcenon::pacs::security::Action::Full, kcenon::pacs::security::Image, kcenon::pacs::security::Metadata, kcenon::pacs::security::Radiologist, kcenon::pacs::security::Action::Read, kcenon::pacs::security::Role, role_permissions_, kcenon::pacs::security::Series, kcenon::pacs::security::Study, kcenon::pacs::security::System, kcenon::pacs::security::Technologist, kcenon::pacs::security::User, kcenon::pacs::security::Viewer, and kcenon::pacs::security::Action::Write.
Referenced by access_control_manager().
◆ map_dicom_operation()
|
staticprivate |
Map DICOM operation to resource type and action.
Definition at line 25 of file access_control_manager.cpp.
References kcenon::pacs::security::CEcho, kcenon::pacs::security::CFind, kcenon::pacs::security::CGet, kcenon::pacs::security::CMove, kcenon::pacs::security::CStore, kcenon::pacs::security::Action::Delete, kcenon::pacs::security::Action::Execute, kcenon::pacs::security::Action::Export, kcenon::pacs::security::Metadata, kcenon::pacs::security::NAction, kcenon::pacs::security::NCreate, kcenon::pacs::security::NDelete, kcenon::pacs::security::NEventReport, kcenon::pacs::security::NGet, kcenon::pacs::security::Action::None, kcenon::pacs::security::NSet, kcenon::pacs::security::Action::Read, kcenon::pacs::security::Study, kcenon::pacs::security::System, and kcenon::pacs::security::Action::Write.
Referenced by check_dicom_operation().
◆ register_ae_title()
| void kcenon::pacs::security::access_control_manager::register_ae_title | ( | std::string_view | ae_title, |
| std::string_view | user_id ) |
Definition at line 242 of file access_control_manager.cpp.
References ae_to_user_id_, and mutex_.
◆ set_audit_callback()
| void kcenon::pacs::security::access_control_manager::set_audit_callback | ( | AccessAuditCallback | callback | ) |
Definition at line 278 of file access_control_manager.cpp.
References audit_callback_, and mutex_.
◆ set_role_permissions()
| void kcenon::pacs::security::access_control_manager::set_role_permissions | ( | Role | role, |
| std::vector< Permission > | permissions ) |
Definition at line 151 of file access_control_manager.cpp.
References role_permissions_.
◆ set_storage()
| void kcenon::pacs::security::access_control_manager::set_storage | ( | std::shared_ptr< security_storage_interface > | storage | ) |
Definition at line 87 of file access_control_manager.cpp.
References storage_.
◆ unregister_ae_title()
| void kcenon::pacs::security::access_control_manager::unregister_ae_title | ( | std::string_view | ae_title | ) |
Definition at line 248 of file access_control_manager.cpp.
References ae_to_user_id_, and mutex_.
◆ validate_access()
|
nodiscard |
Validate access for a user context.
- Parameters
-
ctx User context to validate resource Resource being accessed action_mask Actions being performed
- Returns
- Result with void on success, error on denial
Definition at line 170 of file access_control_manager.cpp.
References kcenon::pacs::security::resource.
Member Data Documentation
◆ ae_to_user_id_
|
private |
Definition at line 144 of file access_control_manager.h.
Referenced by get_context_for_ae(), register_ae_title(), and unregister_ae_title().
◆ audit_callback_
|
private |
Definition at line 145 of file access_control_manager.h.
Referenced by check_dicom_operation(), and set_audit_callback().
◆ mutex_
|
mutableprivate |
Definition at line 146 of file access_control_manager.h.
Referenced by get_context_for_ae(), register_ae_title(), set_audit_callback(), and unregister_ae_title().
◆ role_permissions_
|
private |
Definition at line 142 of file access_control_manager.h.
Referenced by check_permission(), get_role_permissions(), initialize_default_permissions(), and set_role_permissions().
◆ storage_
|
private |
Definition at line 143 of file access_control_manager.h.
Referenced by get_context_for_ae(), and set_storage().
The documentation for this class was generated from the following files:
- include/kcenon/pacs/security/access_control_manager.h
- src/security/access_control_manager.cpp