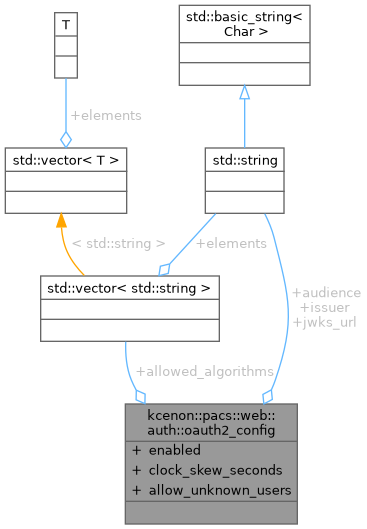
OAuth 2.0 configuration for DICOMweb authorization. More...
#include <oauth2_config.h>
Public Attributes | |
| bool | enabled = false |
| Enable OAuth 2.0 authorization (disabled by default for backward compat) | |
| std::string | issuer |
| Expected token issuer (iss claim). Empty = skip issuer validation. | |
| std::string | audience |
| Expected audience (aud claim). Empty = skip audience validation. | |
| std::string | jwks_url |
| JWKS endpoint URL for public key retrieval. | |
| std::uint32_t | clock_skew_seconds = 60 |
| Allowed clock skew in seconds for exp/nbf validation. | |
| std::vector< std::string > | allowed_algorithms = {"RS256", "ES256"} |
| Allowed signing algorithms (default: RS256, ES256) | |
| bool | allow_unknown_users = false |
| Allow unknown OAuth users not found in RBAC to access as Viewer When false (default): unknown users receive 401 Unauthorized When true: unknown users are granted Role::Viewer (backward compatibility) | |
Detailed Description
OAuth 2.0 configuration for DICOMweb authorization.
When enabled, all DICOMweb endpoints require a valid JWT Bearer token in the Authorization header. When disabled, the system falls back to the existing X-User-ID header-based authentication.
Definition at line 30 of file oauth2_config.h.
Member Data Documentation
◆ allow_unknown_users
| bool kcenon::pacs::web::auth::oauth2_config::allow_unknown_users = false |
Allow unknown OAuth users not found in RBAC to access as Viewer When false (default): unknown users receive 401 Unauthorized When true: unknown users are granted Role::Viewer (backward compatibility)
Definition at line 52 of file oauth2_config.h.
Referenced by kcenon::pacs::web::auth::oauth2_middleware::authenticate().
◆ allowed_algorithms
| std::vector<std::string> kcenon::pacs::web::auth::oauth2_config::allowed_algorithms = {"RS256", "ES256"} |
Allowed signing algorithms (default: RS256, ES256)
Definition at line 47 of file oauth2_config.h.
Referenced by kcenon::pacs::web::auth::jwt_validator::decode().
◆ audience
| std::string kcenon::pacs::web::auth::oauth2_config::audience |
Expected audience (aud claim). Empty = skip audience validation.
Definition at line 38 of file oauth2_config.h.
Referenced by kcenon::pacs::web::auth::jwt_validator::validate_claims().
◆ clock_skew_seconds
| std::uint32_t kcenon::pacs::web::auth::oauth2_config::clock_skew_seconds = 60 |
Allowed clock skew in seconds for exp/nbf validation.
Definition at line 44 of file oauth2_config.h.
Referenced by kcenon::pacs::web::auth::jwt_validator::validate_claims().
◆ enabled
| bool kcenon::pacs::web::auth::oauth2_config::enabled = false |
Enable OAuth 2.0 authorization (disabled by default for backward compat)
Definition at line 32 of file oauth2_config.h.
Referenced by kcenon::pacs::web::auth::oauth2_middleware::enabled().
◆ issuer
| std::string kcenon::pacs::web::auth::oauth2_config::issuer |
Expected token issuer (iss claim). Empty = skip issuer validation.
Definition at line 35 of file oauth2_config.h.
Referenced by kcenon::pacs::web::auth::jwt_validator::validate_claims().
◆ jwks_url
| std::string kcenon::pacs::web::auth::oauth2_config::jwks_url |
JWKS endpoint URL for public key retrieval.
Definition at line 41 of file oauth2_config.h.
The documentation for this struct was generated from the following file:
- include/kcenon/pacs/web/auth/oauth2_config.h