#include <digital_signature.h>
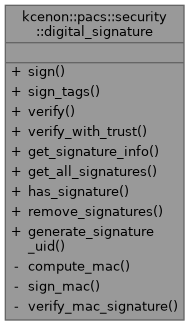
Static Public Member Functions | |
| static auto | sign (core::dicom_dataset &dataset, const certificate &cert, const private_key &key, signature_algorithm algo=signature_algorithm::rsa_sha256) -> kcenon::common::VoidResult |
| Sign a DICOM dataset. | |
| static auto | sign_tags (core::dicom_dataset &dataset, const certificate &cert, const private_key &key, std::span< const core::dicom_tag > tags_to_sign, signature_algorithm algo=signature_algorithm::rsa_sha256) -> kcenon::common::VoidResult |
| Sign specific tags in a DICOM dataset. | |
| static auto | verify (const core::dicom_dataset &dataset) -> kcenon::common::Result< signature_status > |
| Verify digital signatures in a dataset. | |
| static auto | verify_with_trust (const core::dicom_dataset &dataset, const std::vector< certificate > &trusted_certs) -> kcenon::common::Result< signature_status > |
| Verify digital signatures with a trusted certificate store. | |
| static auto | get_signature_info (const core::dicom_dataset &dataset) -> std::optional< signature_info > |
| Get information about signatures in a dataset. | |
| static auto | get_all_signatures (const core::dicom_dataset &dataset) -> std::vector< signature_info > |
| Get all signatures in a dataset. | |
| static auto | has_signature (const core::dicom_dataset &dataset) -> bool |
| Check if a dataset contains digital signatures. | |
| static auto | remove_signatures (core::dicom_dataset &dataset) -> bool |
| Remove all digital signatures from a dataset. | |
| static auto | generate_signature_uid () -> std::string |
| Generate a new Digital Signature UID. | |
Static Private Member Functions | |
| static auto | compute_mac (const core::dicom_dataset &dataset, std::span< const core::dicom_tag > tags, mac_algorithm algo) -> std::vector< std::uint8_t > |
| static auto | sign_mac (std::span< const std::uint8_t > mac_data, const private_key &key, signature_algorithm algo) -> kcenon::common::Result< std::vector< std::uint8_t > > |
| static auto | verify_mac_signature (std::span< const std::uint8_t > mac_data, std::span< const std::uint8_t > signature, const certificate &cert, signature_algorithm algo) -> bool |
Detailed Description
Definition at line 68 of file digital_signature.h.
Member Function Documentation
◆ compute_mac()
|
staticprivate |
Definition at line 602 of file digital_signature.cpp.
◆ generate_signature_uid()
|
staticnodiscard |
Generate a new Digital Signature UID.
Creates a new unique identifier for a digital signature.
- Returns
- New UID string
Definition at line 598 of file digital_signature.cpp.
◆ get_all_signatures()
|
staticnodiscard |
Get all signatures in a dataset.
Extracts information for all signatures if multiple are present.
- Parameters
-
dataset The dataset to inspect
- Returns
- Vector of signature info (empty if no signatures)
Definition at line 556 of file digital_signature.cpp.
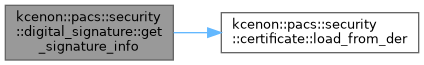
◆ get_signature_info()
|
staticnodiscard |
Get information about signatures in a dataset.
Extracts signature metadata from the Digital Signature Sequence without performing verification.
- Parameters
-
dataset The dataset to inspect
- Returns
- Optional containing signature info, or nullopt if no signature
Definition at line 506 of file digital_signature.cpp.
References kcenon::pacs::security::certificate::load_from_der(), and kcenon::pacs::security::rsa_sha256.
◆ has_signature()
|
staticnodiscard |
Check if a dataset contains digital signatures.
- Parameters
-
dataset The dataset to check
- Returns
- true if Digital Signature Sequence is present
Definition at line 570 of file digital_signature.cpp.
◆ remove_signatures()
|
static |
Remove all digital signatures from a dataset.
Removes the Digital Signature Sequence (0400,0561) from the dataset.
- Parameters
-
dataset The dataset to modify
- Returns
- true if signatures were removed, false if none present
Definition at line 578 of file digital_signature.cpp.
◆ sign()
|
staticnodiscard |
Sign a DICOM dataset.
Creates a digital signature for the entire dataset and adds the Digital Signature Sequence (0400,0561) to the dataset.
- Parameters
-
dataset The dataset to sign (modified in place) cert Signer's X.509 certificate key Signer's private key (must match certificate's public key) algo Signature algorithm to use (default: RSA-SHA256)
- Returns
- Result indicating success or error
- Note
- The dataset is modified to include the signature sequence.
- All existing data elements are signed by default.
Definition at line 289 of file digital_signature.cpp.
◆ sign_mac()
|
staticprivate |
Definition at line 637 of file digital_signature.cpp.
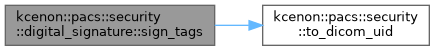
◆ sign_tags()
|
staticnodiscard |
Sign specific tags in a DICOM dataset.
Creates a digital signature for only the specified tags.
- Parameters
-
dataset The dataset to sign (modified in place) cert Signer's X.509 certificate key Signer's private key tags_to_sign List of tags to include in signature algo Signature algorithm to use
- Returns
- Result indicating success or error
Definition at line 300 of file digital_signature.cpp.
References kcenon::pacs::encoding::AT, kcenon::pacs::encoding::CS, kcenon::pacs::encoding::DT, kcenon::pacs::encoding::OB, kcenon::pacs::security::to_dicom_uid(), and kcenon::pacs::encoding::UI.
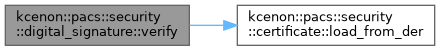
◆ verify()
|
staticnodiscard |
Verify digital signatures in a dataset.
Verifies all digital signatures present in the Digital Signature Sequence (0400,0561).
- Parameters
-
dataset The dataset to verify
- Returns
- Result containing signature status or error
- Note
- Returns signature_status::no_signature if no signatures present.
- Returns signature_status::invalid if any signature fails verification.
Definition at line 389 of file digital_signature.cpp.
References kcenon::pacs::security::expired, kcenon::pacs::security::invalid, kcenon::pacs::security::certificate::load_from_der(), kcenon::pacs::security::no_signature, kcenon::pacs::security::sha256, kcenon::pacs::security::untrusted_signer, and kcenon::pacs::security::valid.
◆ verify_mac_signature()
|
staticprivate |
Definition at line 695 of file digital_signature.cpp.
◆ verify_with_trust()
|
staticnodiscard |
Verify digital signatures with a trusted certificate store.
Verifies signatures and validates the signer's certificate against a set of trusted certificates.
- Parameters
-
dataset The dataset to verify trusted_certs Trusted certificates for validation
- Returns
- Result containing signature status or error
Definition at line 467 of file digital_signature.cpp.
References kcenon::pacs::security::certificate::load_from_der(), kcenon::pacs::security::untrusted_signer, and kcenon::pacs::security::valid.
The documentation for this class was generated from the following files:
- include/kcenon/pacs/security/digital_signature.h
- src/security/digital_signature.cpp