QUIC-TLS integration handler (RFC 9001) More...
#include <crypto.h>
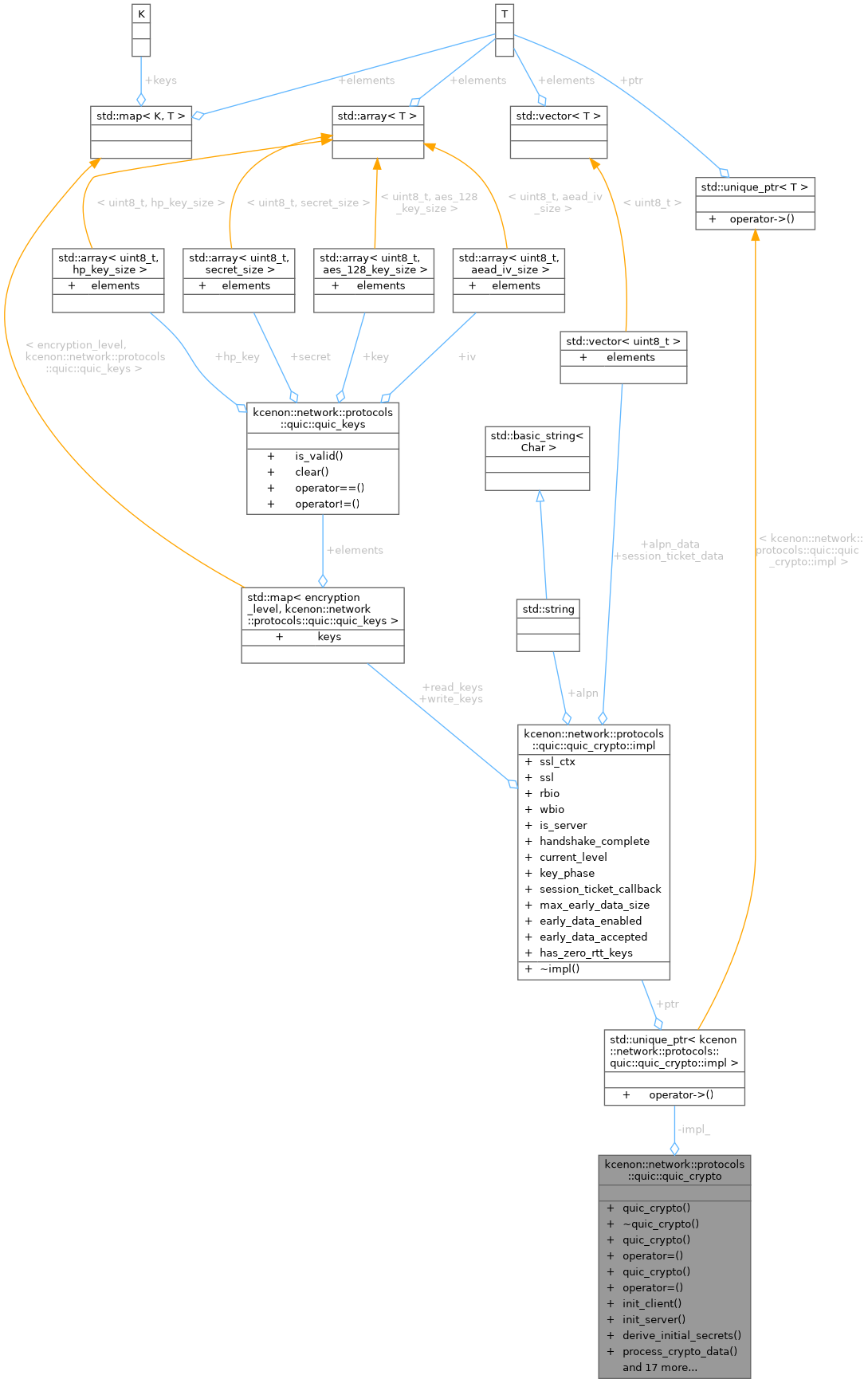
Classes | |
| struct | impl |
Public Types | |
| using | session_ticket_callback_t |
| Callback type for receiving session tickets. | |
Public Member Functions | |
| quic_crypto () | |
| Default constructor. | |
| ~quic_crypto () | |
| Destructor (cleans up OpenSSL resources) | |
| quic_crypto (const quic_crypto &)=delete | |
| quic_crypto & | operator= (const quic_crypto &)=delete |
| quic_crypto (quic_crypto &&other) noexcept | |
| quic_crypto & | operator= (quic_crypto &&other) noexcept |
| auto | init_client (const std::string &server_name) -> VoidResult |
| Initialize as client. | |
| auto | init_server (const std::string &cert_file, const std::string &key_file) -> VoidResult |
| Initialize as server. | |
| auto | derive_initial_secrets (const connection_id &dest_cid) -> VoidResult |
| Derive initial secrets from destination connection ID. | |
| auto | process_crypto_data (encryption_level level, std::span< const uint8_t > data) -> Result< std::vector< uint8_t > > |
| Process incoming CRYPTO frame data. | |
| auto | start_handshake () -> Result< std::vector< uint8_t > > |
| Start the handshake (generate initial CRYPTO data) | |
| auto | is_handshake_complete () const noexcept -> bool |
| Check if the handshake is complete. | |
| auto | current_level () const noexcept -> encryption_level |
| Get current encryption level. | |
| auto | get_write_keys (encryption_level level) const -> Result< quic_keys > |
| Get write keys for an encryption level. | |
| auto | get_read_keys (encryption_level level) const -> Result< quic_keys > |
| Get read keys for an encryption level. | |
| void | set_keys (encryption_level level, const quic_keys &read_keys, const quic_keys &write_keys) |
| Set keys for an encryption level (used during handshake) | |
| auto | update_keys () -> VoidResult |
| Perform a key update (1-RTT only) | |
| auto | get_alpn () const -> std::string |
| Get the negotiated ALPN protocol. | |
| auto | set_alpn (const std::vector< std::string > &protocols) -> VoidResult |
| Set ALPN protocols to offer/accept. | |
| auto | is_server () const noexcept -> bool |
| Check if this is a server instance. | |
| auto | key_phase () const noexcept -> uint8_t |
| Get current key phase (for key updates) | |
| void | set_session_ticket_callback (session_ticket_callback_t cb) |
| Set callback for receiving session tickets. | |
| auto | set_session_ticket (std::span< const uint8_t > ticket_data) -> VoidResult |
| Set a session ticket for 0-RTT resumption. | |
| auto | enable_early_data (uint32_t max_early_data) -> VoidResult |
| Enable 0-RTT early data. | |
| auto | is_early_data_accepted () const noexcept -> bool |
| Check if 0-RTT early data was accepted by the server. | |
| auto | derive_zero_rtt_keys () -> VoidResult |
| Derive 0-RTT keys from session ticket. | |
| auto | has_zero_rtt_keys () const noexcept -> bool |
| Check if 0-RTT keys are available. | |
Private Attributes | |
| std::unique_ptr< impl > | impl_ |
Detailed Description
QUIC-TLS integration handler (RFC 9001)
Manages the TLS 1.3 handshake for QUIC, handling:
- Key derivation for each encryption level
- CRYPTO frame data processing
- Key updates after handshake
This class wraps OpenSSL for cryptographic operations.
Member Typedef Documentation
◆ session_ticket_callback_t
Callback type for receiving session tickets.
This callback is invoked when a NewSessionTicket message is received from the server after handshake completion.
- Parameters
-
ticket_data Raw session ticket data lifetime_hint Ticket lifetime in seconds ticket_age_add Obfuscation value for ticket age max_early_data Maximum early data size (0 if early data not allowed)
Constructor & Destructor Documentation
◆ quic_crypto() [1/3]
| kcenon::network::protocols::quic::quic_crypto::quic_crypto | ( | ) |
Default constructor.
Definition at line 772 of file crypto.cpp.
◆ ~quic_crypto()
|
default |
Destructor (cleans up OpenSSL resources)
◆ quic_crypto() [2/3]
|
delete |
◆ quic_crypto() [3/3]
|
defaultnoexcept |
Member Function Documentation
◆ current_level()
|
nodiscardnoexcept |
Get current encryption level.
- Returns
- Current encryption level
Definition at line 1008 of file crypto.cpp.
References kcenon::network::protocols::quic::quic_crypto::impl::current_level, and impl_.
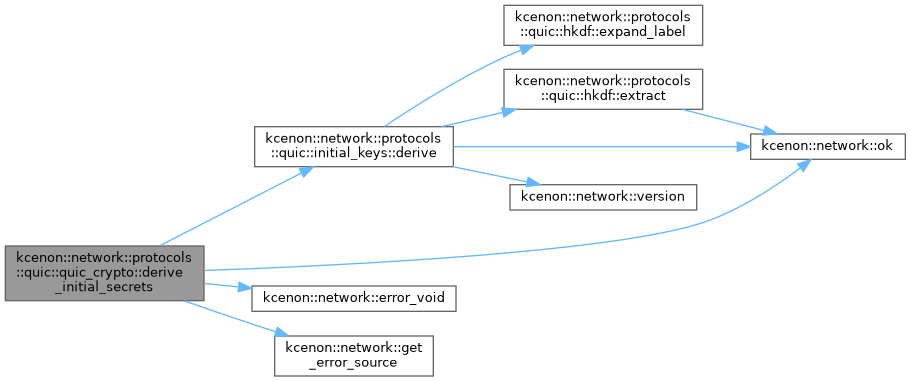
◆ derive_initial_secrets()
|
nodiscard |
Derive initial secrets from destination connection ID.
- Parameters
-
dest_cid Destination Connection ID
- Returns
- Success or error
Definition at line 883 of file crypto.cpp.
References kcenon::network::protocols::quic::initial_keys::derive(), kcenon::network::error_void(), kcenon::network::get_error_source(), kcenon::network::protocols::quic::initial, and kcenon::network::ok().
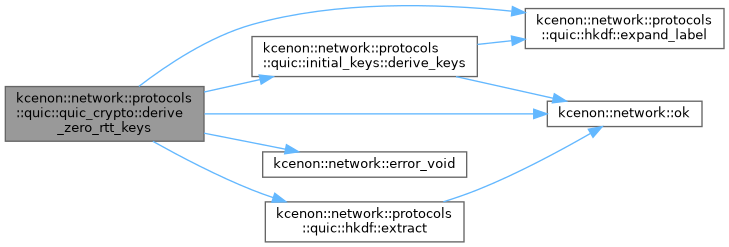
◆ derive_zero_rtt_keys()
|
nodiscard |
Derive 0-RTT keys from session ticket.
- Returns
- Success or error
Called internally when a valid session ticket is set.
Definition at line 1182 of file crypto.cpp.
References kcenon::network::protocols::quic::initial_keys::derive_keys(), kcenon::network::error_void(), kcenon::network::protocols::quic::hkdf::expand_label(), kcenon::network::protocols::quic::hkdf::extract(), kcenon::network::protocols::quic::initial_salt_v1, kcenon::network::ok(), kcenon::network::protocols::quic::secret_size, and kcenon::network::protocols::quic::zero_rtt.
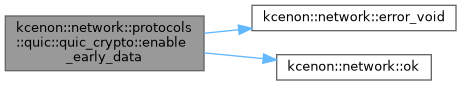
◆ enable_early_data()
|
nodiscard |
Enable 0-RTT early data.
- Parameters
-
max_early_data Maximum bytes of early data to send
- Returns
- Success or error
Must be called after set_session_ticket() and before init_client().
Definition at line 1163 of file crypto.cpp.
References kcenon::network::error_void(), and kcenon::network::ok().
◆ get_alpn()
|
nodiscard |
Get the negotiated ALPN protocol.
- Returns
- ALPN protocol string or empty if not negotiated
Definition at line 1097 of file crypto.cpp.
References kcenon::network::protocols::quic::quic_crypto::impl::alpn, and impl_.
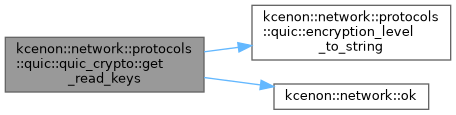
◆ get_read_keys()
|
nodiscard |
Get read keys for an encryption level.
- Parameters
-
level Desired encryption level
- Returns
- Keys or error if not available
Definition at line 1026 of file crypto.cpp.
References kcenon::network::protocols::quic::encryption_level_to_string(), kcenon::network::protocols::quic::error, and kcenon::network::ok().
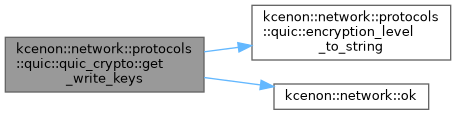
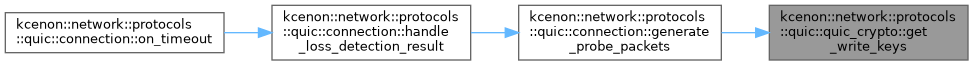
◆ get_write_keys()
|
nodiscard |
Get write keys for an encryption level.
- Parameters
-
level Desired encryption level
- Returns
- Keys or error if not available
Definition at line 1013 of file crypto.cpp.
References kcenon::network::protocols::quic::encryption_level_to_string(), kcenon::network::protocols::quic::error, and kcenon::network::ok().
Referenced by kcenon::network::protocols::quic::connection::generate_probe_packets().
◆ has_zero_rtt_keys()
|
nodiscardnoexcept |
Check if 0-RTT keys are available.
- Returns
- true if 0-RTT keys have been derived
Definition at line 1265 of file crypto.cpp.
References kcenon::network::protocols::quic::quic_crypto::impl::has_zero_rtt_keys, and impl_.
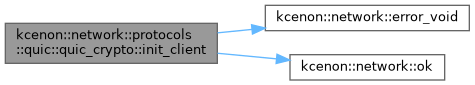
◆ init_client()
|
nodiscard |
Initialize as client.
- Parameters
-
server_name Server hostname (for SNI)
- Returns
- Success or error
Definition at line 782 of file crypto.cpp.
References kcenon::network::error_void(), and kcenon::network::ok().
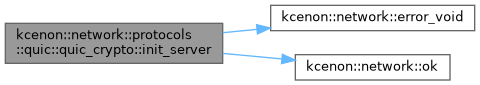
◆ init_server()
|
nodiscard |
Initialize as server.
- Parameters
-
cert_file Path to certificate file (PEM format) key_file Path to private key file (PEM format)
- Returns
- Success or error
Definition at line 827 of file crypto.cpp.
References kcenon::network::error_void(), and kcenon::network::ok().
◆ is_early_data_accepted()
|
nodiscardnoexcept |
Check if 0-RTT early data was accepted by the server.
- Returns
- true if server accepted early data, false otherwise
This value is only meaningful after handshake completion.
Definition at line 1177 of file crypto.cpp.
References kcenon::network::protocols::quic::quic_crypto::impl::early_data_accepted, and impl_.
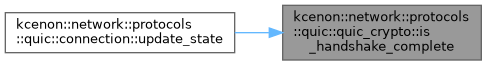
◆ is_handshake_complete()
|
nodiscardnoexcept |
Check if the handshake is complete.
- Returns
- true if handshake has finished successfully
Definition at line 1003 of file crypto.cpp.
References kcenon::network::protocols::quic::quic_crypto::impl::handshake_complete, and impl_.
Referenced by kcenon::network::protocols::quic::connection::update_state().
◆ is_server()
|
nodiscardnoexcept |
Check if this is a server instance.
- Returns
- true if server, false if client
Definition at line 1132 of file crypto.cpp.
References impl_, and kcenon::network::protocols::quic::quic_crypto::impl::is_server.
◆ key_phase()
|
nodiscardnoexcept |
Get current key phase (for key updates)
- Returns
- Current key phase (0 or 1)
Definition at line 1137 of file crypto.cpp.
References impl_, and kcenon::network::protocols::quic::quic_crypto::impl::key_phase.
◆ operator=() [1/2]
|
delete |
◆ operator=() [2/2]
|
defaultnoexcept |
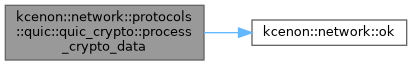
◆ process_crypto_data()
|
nodiscard |
Process incoming CRYPTO frame data.
- Parameters
-
level Encryption level of the data data CRYPTO frame payload
- Returns
- Outgoing CRYPTO data to send (may be empty) or error
Definition at line 912 of file crypto.cpp.
References kcenon::network::protocols::quic::application, kcenon::network::protocols::quic::error, and kcenon::network::ok().
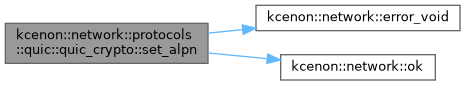
◆ set_alpn()
|
nodiscard |
Set ALPN protocols to offer/accept.
- Parameters
-
protocols List of protocol names (e.g., {"h3", "hq-interop"})
- Returns
- Success or error
Definition at line 1102 of file crypto.cpp.
References kcenon::network::error_void(), and kcenon::network::ok().
◆ set_keys()
| void kcenon::network::protocols::quic::quic_crypto::set_keys | ( | encryption_level | level, |
| const quic_keys & | read_keys, | ||
| const quic_keys & | write_keys ) |
Set keys for an encryption level (used during handshake)
- Parameters
-
level Encryption level read_keys Keys for decryption write_keys Keys for encryption
Definition at line 1039 of file crypto.cpp.
References kcenon::network::protocols::quic::quic_crypto::impl::current_level, impl_, kcenon::network::protocols::quic::quic_crypto::impl::read_keys, and kcenon::network::protocols::quic::quic_crypto::impl::write_keys.
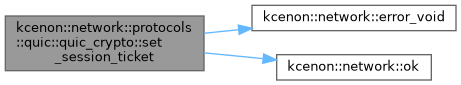
◆ set_session_ticket()
|
nodiscard |
Set a session ticket for 0-RTT resumption.
- Parameters
-
ticket_data Session ticket from previous connection
- Returns
- Success or error
Must be called before init_client() for the ticket to be used.
Definition at line 1151 of file crypto.cpp.
References kcenon::network::error_void(), and kcenon::network::ok().
◆ set_session_ticket_callback()
| void kcenon::network::protocols::quic::quic_crypto::set_session_ticket_callback | ( | session_ticket_callback_t | cb | ) |
Set callback for receiving session tickets.
- Parameters
-
cb Callback function
The callback will be invoked on the I/O thread when a NewSessionTicket message is received from the server.
Definition at line 1146 of file crypto.cpp.
References impl_, and kcenon::network::protocols::quic::quic_crypto::impl::session_ticket_callback.
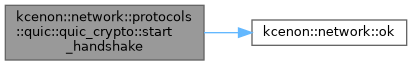
◆ start_handshake()
|
nodiscard |
Start the handshake (generate initial CRYPTO data)
- Returns
- Initial CRYPTO data to send or error
Definition at line 965 of file crypto.cpp.
References kcenon::network::protocols::quic::error, and kcenon::network::ok().
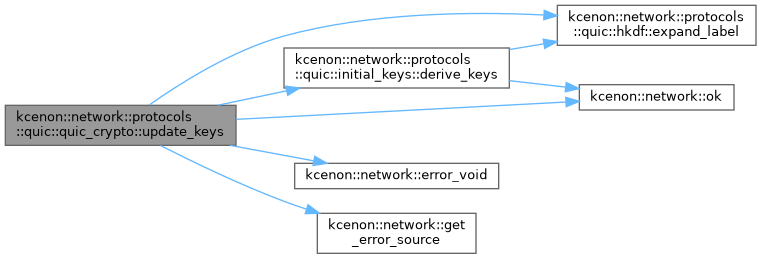
◆ update_keys()
|
nodiscard |
Perform a key update (1-RTT only)
- Returns
- Success or error
Definition at line 1052 of file crypto.cpp.
References kcenon::network::protocols::quic::application, kcenon::network::protocols::quic::initial_keys::derive_keys(), kcenon::network::error_void(), kcenon::network::protocols::quic::hkdf::expand_label(), kcenon::network::get_error_source(), kcenon::network::ok(), and kcenon::network::protocols::quic::secret_size.
Member Data Documentation
◆ impl_
|
private |
Definition at line 448 of file crypto.h.
Referenced by current_level(), get_alpn(), has_zero_rtt_keys(), is_early_data_accepted(), is_handshake_complete(), is_server(), key_phase(), set_keys(), and set_session_ticket_callback().
The documentation for this class was generated from the following files:
- src/internal/protocols/quic/crypto.h
- src/protocols/quic/crypto.cpp