HKDF (HMAC-based Key Derivation Function) utilities (RFC 5869) More...
#include <crypto.h>
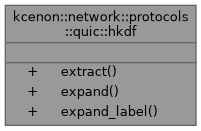
Static Public Member Functions | |
| static auto | extract (std::span< const uint8_t > salt, std::span< const uint8_t > ikm) -> Result< std::array< uint8_t, secret_size > > |
| HKDF-Extract function. | |
| static auto | expand (std::span< const uint8_t > prk, std::span< const uint8_t > info, size_t length) -> Result< std::vector< uint8_t > > |
| HKDF-Expand function. | |
| static auto | expand_label (std::span< const uint8_t > secret, const std::string &label, std::span< const uint8_t > context, size_t length) -> Result< std::vector< uint8_t > > |
| HKDF-Expand-Label function (TLS 1.3 style) | |
Detailed Description
HKDF (HMAC-based Key Derivation Function) utilities (RFC 5869)
Used for deriving QUIC keys from secrets.
Member Function Documentation
◆ expand()
|
staticnodiscard |
HKDF-Expand function.
- Parameters
-
prk Pseudorandom key from Extract info Context and application specific information length Desired output length
- Returns
- Output keying material (OKM) or error
Definition at line 124 of file crypto.cpp.
References kcenon::network::protocols::quic::error, and kcenon::network::ok().
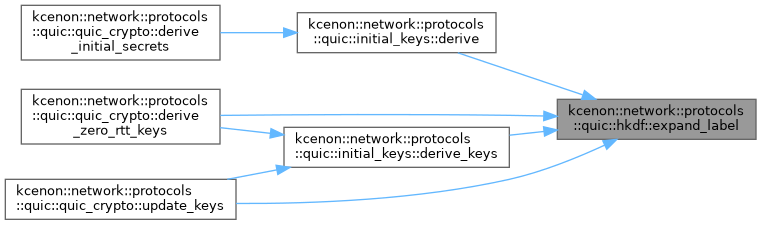
◆ expand_label()
|
staticnodiscard |
HKDF-Expand-Label function (TLS 1.3 style)
- Parameters
-
secret Secret to expand label Label string (without "tls13 " prefix) context Context data (usually empty for QUIC) length Desired output length
- Returns
- Output keying material or error
Definition at line 193 of file crypto.cpp.
Referenced by kcenon::network::protocols::quic::initial_keys::derive(), kcenon::network::protocols::quic::initial_keys::derive_keys(), kcenon::network::protocols::quic::quic_crypto::derive_zero_rtt_keys(), and kcenon::network::protocols::quic::quic_crypto::update_keys().
◆ extract()
|
staticnodiscard |
HKDF-Extract function.
- Parameters
-
salt Salt value (non-secret random value) ikm Input keying material
- Returns
- Pseudorandom key (PRK) or error
Definition at line 56 of file crypto.cpp.
References kcenon::network::protocols::quic::error, and kcenon::network::ok().
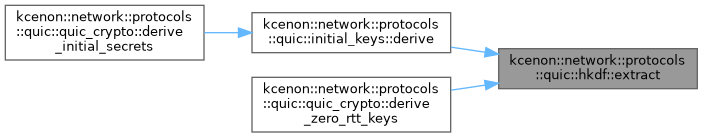
Referenced by kcenon::network::protocols::quic::initial_keys::derive(), and kcenon::network::protocols::quic::quic_crypto::derive_zero_rtt_keys().
The documentation for this class was generated from the following files:
- src/internal/protocols/quic/crypto.h
- src/protocols/quic/crypto.cpp