Derives initial encryption keys from Destination Connection ID. More...
#include <crypto.h>
Static Public Member Functions | |
| static auto | derive (const connection_id &dest_cid, uint32_t version=0x00000001) -> Result< key_pair > |
| Derive client and server initial keys. | |
| static auto | derive_keys (std::span< const uint8_t > initial_secret, bool is_client_keys) -> Result< quic_keys > |
| Derive keys from an initial secret. | |
Detailed Description
Derives initial encryption keys from Destination Connection ID.
Initial keys are derived deterministically from the Destination Connection ID, allowing peers to decrypt Initial packets without a prior handshake.
Member Function Documentation
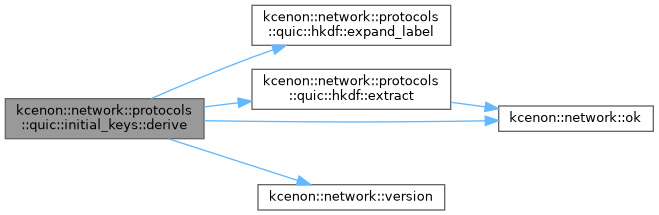
◆ derive()
|
staticnodiscard |
Derive client and server initial keys.
- Parameters
-
dest_cid Destination Connection ID (from client's perspective) version QUIC version (affects salt selection)
- Returns
- Key pair for initial encryption level or error
Definition at line 237 of file crypto.cpp.
References kcenon::network::protocols::quic::error, kcenon::network::protocols::quic::hkdf::expand_label(), kcenon::network::protocols::quic::hkdf::extract(), kcenon::network::protocols::quic::initial_salt_v1, kcenon::network::protocols::quic::initial_salt_v2, kcenon::network::ok(), kcenon::network::protocols::quic::key_pair::read, kcenon::network::protocols::quic::secret_size, kcenon::network::version(), kcenon::network::protocols::quic::quic_version::version_2, and kcenon::network::protocols::quic::key_pair::write.
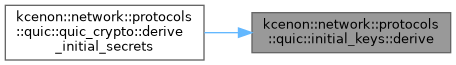
Referenced by kcenon::network::protocols::quic::quic_crypto::derive_initial_secrets().
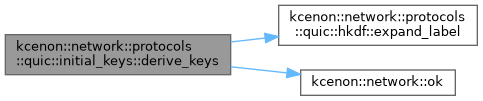
◆ derive_keys()
|
staticnodiscard |
Derive keys from an initial secret.
- Parameters
-
initial_secret The initial secret is_client_keys true for client keys, false for server keys
- Returns
- QUIC keys or error
Definition at line 339 of file crypto.cpp.
References kcenon::network::protocols::quic::aead_iv_size, kcenon::network::protocols::quic::aes_128_key_size, kcenon::network::protocols::quic::error, kcenon::network::protocols::quic::hkdf::expand_label(), kcenon::network::protocols::quic::quic_keys::hp_key, kcenon::network::protocols::quic::hp_key_size, kcenon::network::protocols::quic::quic_keys::iv, kcenon::network::protocols::quic::quic_keys::key, and kcenon::network::ok().
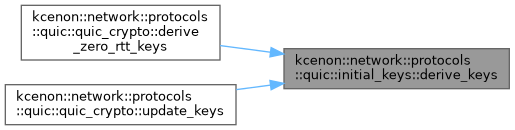
Referenced by kcenon::network::protocols::quic::quic_crypto::derive_zero_rtt_keys(), and kcenon::network::protocols::quic::quic_crypto::update_keys().
The documentation for this class was generated from the following files:
- src/internal/protocols/quic/crypto.h
- src/protocols/quic/crypto.cpp