TLS Integration Tests - Secure DICOM Communication. More...
#include "test_fixtures.h"#include <catch2/catch_test_macros.hpp>#include <catch2/matchers/catch_matchers_string.hpp>#include "kcenon/pacs/integration/network_adapter.h"#include "kcenon/pacs/network/dimse/dimse_message.h"#include "kcenon/pacs/services/verification_scp.h"#include <filesystem>#include <thread>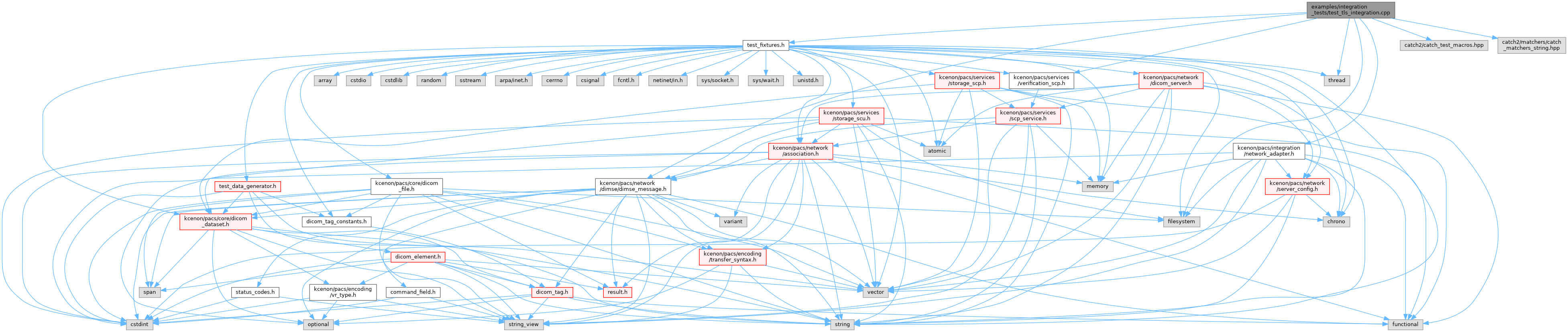
Go to the source code of this file.
Functions | |
| TEST_CASE ("TLS C-ECHO connection", "[tls][connectivity]") | |
| TEST_CASE ("TLS certificate validation", "[tls][security]") | |
| TEST_CASE ("Mutual TLS authentication", "[tls][mtls]") | |
| TEST_CASE ("TLS version negotiation", "[tls][version]") | |
| TEST_CASE ("Multiple concurrent TLS connections", "[tls][concurrent]") | |
| TEST_CASE ("TLS configuration validation", "[tls][config]") | |
Detailed Description
TLS Integration Tests - Secure DICOM Communication.
Tests TLS-secured DICOM communication using the secure_dicom example applications and network_adapter TLS configuration.
- See also
- Issue #141 - TLS Integration Tests
- DICOM PS3.15 - Security and System Management Profiles
Test Scenarios:
- Basic TLS connection
- Certificate validation
- Mutual TLS (mTLS)
- TLS-secured store/query workflow
Definition in file test_tls_integration.cpp.
Function Documentation
◆ TEST_CASE() [1/6]
| TEST_CASE | ( | "Multiple concurrent TLS connections" | , |
| "" | [tls][concurrent] ) |
Definition at line 598 of file test_tls_integration.cpp.
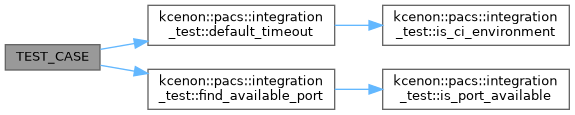
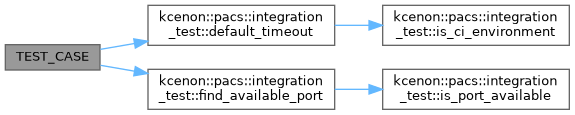
References kcenon::pacs::integration::tls_config::ca_path, kcenon::pacs::integration::tls_config::cert_path, kcenon::pacs::integration_test::default_timeout(), kcenon::pacs::integration::tls_config::enabled, kcenon::pacs::integration_test::find_available_port(), kcenon::pacs::integration::tls_config::key_path, kcenon::pacs::integration::tls_config::min_version, kcenon::pacs::services::verification_sop_class_uid, and kcenon::pacs::integration::tls_config::verify_peer.
◆ TEST_CASE() [2/6]
| TEST_CASE | ( | "Mutual TLS authentication" | , |
| "" | [tls][mtls] ) |
Definition at line 406 of file test_tls_integration.cpp.
References kcenon::pacs::integration::tls_config::ca_path, kcenon::pacs::integration::tls_config::cert_path, kcenon::pacs::integration_test::default_timeout(), kcenon::pacs::integration::tls_config::enabled, kcenon::pacs::integration_test::find_available_port(), kcenon::pacs::integration::tls_config::key_path, kcenon::pacs::integration::tls_config::min_version, kcenon::pacs::services::verification_sop_class_uid, and kcenon::pacs::integration::tls_config::verify_peer.
◆ TEST_CASE() [3/6]
| TEST_CASE | ( | "TLS C-ECHO connection" | , |
| "" | [tls][connectivity] ) |
Definition at line 247 of file test_tls_integration.cpp.
References kcenon::pacs::integration::tls_config::ca_path, kcenon::pacs::integration::tls_config::cert_path, kcenon::pacs::integration_test::default_timeout(), kcenon::pacs::integration::tls_config::enabled, kcenon::pacs::integration_test::find_available_port(), kcenon::pacs::integration::tls_config::key_path, kcenon::pacs::integration::tls_config::min_version, kcenon::pacs::services::verification_sop_class_uid, and kcenon::pacs::integration::tls_config::verify_peer.
◆ TEST_CASE() [4/6]
| TEST_CASE | ( | "TLS certificate validation" | , |
| "" | [tls][security] ) |
Definition at line 320 of file test_tls_integration.cpp.
References kcenon::pacs::integration::tls_config::ca_path, kcenon::pacs::integration::tls_config::cert_path, kcenon::pacs::integration_test::default_timeout(), kcenon::pacs::integration::tls_config::enabled, kcenon::pacs::integration_test::find_available_port(), kcenon::pacs::integration::tls_config::key_path, kcenon::pacs::integration::tls_config::min_version, and kcenon::pacs::integration::tls_config::verify_peer.
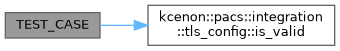
◆ TEST_CASE() [5/6]
| TEST_CASE | ( | "TLS configuration validation" | , |
| "" | [tls][config] ) |
Definition at line 681 of file test_tls_integration.cpp.
References kcenon::pacs::integration::tls_config::ca_path, kcenon::pacs::integration::tls_config::cert_path, kcenon::pacs::integration::tls_config::enabled, kcenon::pacs::integration::tls_config::is_valid(), and kcenon::pacs::integration::tls_config::key_path.
◆ TEST_CASE() [6/6]
| TEST_CASE | ( | "TLS version negotiation" | , |
| "" | [tls][version] ) |
Definition at line 513 of file test_tls_integration.cpp.
References kcenon::pacs::integration::tls_config::ca_path, kcenon::pacs::integration::tls_config::cert_path, kcenon::pacs::integration_test::default_timeout(), kcenon::pacs::integration::tls_config::enabled, kcenon::pacs::integration_test::find_available_port(), kcenon::pacs::integration::tls_config::key_path, kcenon::pacs::integration::tls_config::min_version, and kcenon::pacs::integration::tls_config::verify_peer.