QUIC packet protection (encryption/decryption) (RFC 9001 Section 5) More...
#include <crypto.h>
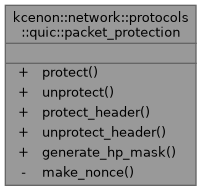
Static Public Member Functions | |
| static auto | protect (const quic_keys &keys, std::span< const uint8_t > header, std::span< const uint8_t > payload, uint64_t packet_number) -> Result< std::vector< uint8_t > > |
| Protect (encrypt) a QUIC packet. | |
| static auto | unprotect (const quic_keys &keys, std::span< const uint8_t > packet, size_t header_length, uint64_t packet_number) -> Result< std::pair< std::vector< uint8_t >, std::vector< uint8_t > > > |
| Unprotect (decrypt) a QUIC packet. | |
| static auto | protect_header (const quic_keys &keys, std::span< uint8_t > header, size_t pn_offset, size_t pn_length, std::span< const uint8_t > sample) -> VoidResult |
| Apply header protection. | |
| static auto | unprotect_header (const quic_keys &keys, std::span< uint8_t > header, size_t pn_offset, std::span< const uint8_t > sample) -> Result< std::pair< uint8_t, size_t > > |
| Remove header protection. | |
| static auto | generate_hp_mask (std::span< const uint8_t > hp_key, std::span< const uint8_t > sample) -> Result< std::array< uint8_t, 5 > > |
| Generate header protection mask using AES-ECB. | |
Static Private Member Functions | |
| static auto | make_nonce (std::span< const uint8_t > iv, uint64_t packet_number) -> std::array< uint8_t, aead_iv_size > |
| Construct nonce from IV and packet number. | |
Detailed Description
QUIC packet protection (encryption/decryption) (RFC 9001 Section 5)
Provides AEAD encryption for packet payloads and header protection to prevent linkability attacks.
Member Function Documentation
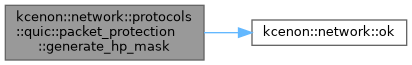
◆ generate_hp_mask()
|
staticnodiscard |
Generate header protection mask using AES-ECB.
- Parameters
-
hp_key Header protection key sample 16-byte sample from ciphertext
- Returns
- 5-byte mask or error
Definition at line 598 of file crypto.cpp.
References kcenon::network::protocols::quic::error, kcenon::network::protocols::quic::hp_sample_size, and kcenon::network::ok().
◆ make_nonce()
|
staticnodiscardprivate |
Construct nonce from IV and packet number.
- Parameters
-
iv Initialization vector packet_number Packet number
- Returns
- Nonce for AEAD
Definition at line 408 of file crypto.cpp.
References kcenon::network::protocols::quic::aead_iv_size.
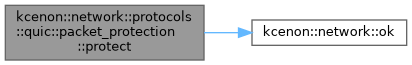
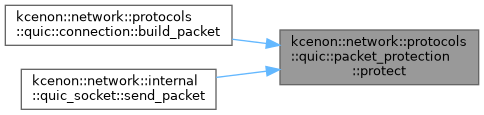
◆ protect()
|
staticnodiscard |
Protect (encrypt) a QUIC packet.
- Parameters
-
keys Encryption keys for the current level header Packet header (will be used as AAD) payload Plaintext payload to encrypt packet_number Packet number (used for nonce derivation)
- Returns
- Protected packet (header + encrypted payload + tag) or error
Definition at line 425 of file crypto.cpp.
References kcenon::network::protocols::quic::aead_tag_size, kcenon::network::protocols::quic::error, and kcenon::network::ok().
Referenced by kcenon::network::protocols::quic::connection::build_packet(), and kcenon::network::internal::quic_socket::send_packet().
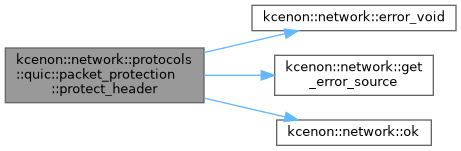
◆ protect_header()
|
staticnodiscard |
Apply header protection.
- Parameters
-
keys Keys containing the HP key header Header bytes (modified in place) pn_offset Offset of packet number in header pn_length Length of packet number (1-4) sample Sample from encrypted payload (16 bytes)
- Returns
- Success or error
Definition at line 649 of file crypto.cpp.
References kcenon::network::error_void(), kcenon::network::get_error_source(), and kcenon::network::ok().
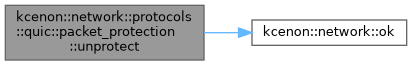
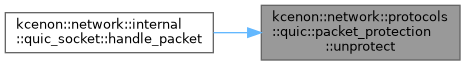
◆ unprotect()
|
staticnodiscard |
Unprotect (decrypt) a QUIC packet.
- Parameters
-
keys Decryption keys for the current level packet Full packet data (header + encrypted payload + tag) header_length Length of the header (including packet number) packet_number Decoded packet number
- Returns
- Pair of (header, decrypted payload) or error
Definition at line 508 of file crypto.cpp.
References kcenon::network::protocols::quic::aead_tag_size, kcenon::network::protocols::quic::error, and kcenon::network::ok().
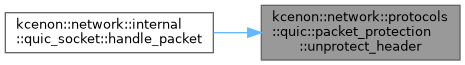
Referenced by kcenon::network::internal::quic_socket::handle_packet().
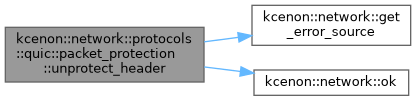
◆ unprotect_header()
|
staticnodiscard |
Remove header protection.
- Parameters
-
keys Keys containing the HP key header Header bytes (modified in place) pn_offset Offset of packet number in header sample Sample from encrypted payload (16 bytes)
- Returns
- Pair of (first_byte_unprotected, pn_length) or error
Definition at line 687 of file crypto.cpp.
References kcenon::network::protocols::quic::error, kcenon::network::get_error_source(), and kcenon::network::ok().
Referenced by kcenon::network::internal::quic_socket::handle_packet().
The documentation for this class was generated from the following files:
- src/internal/protocols/quic/crypto.h
- src/protocols/quic/crypto.cpp