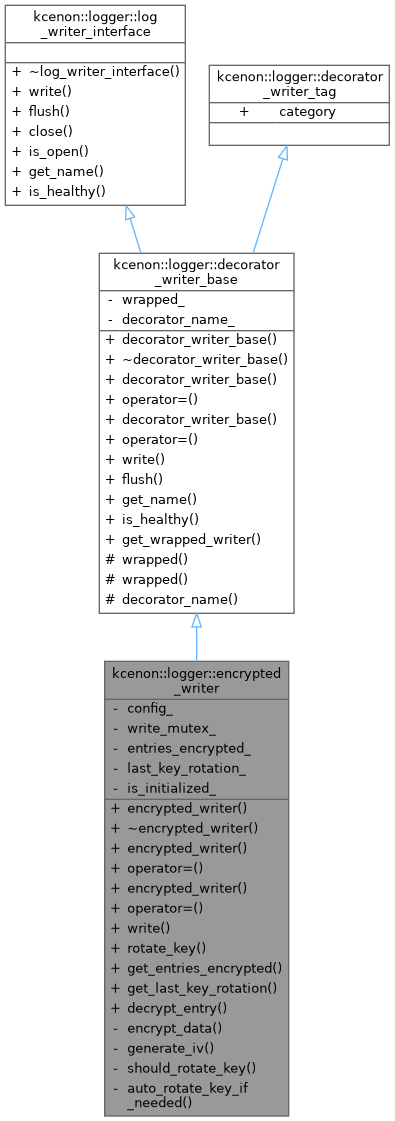
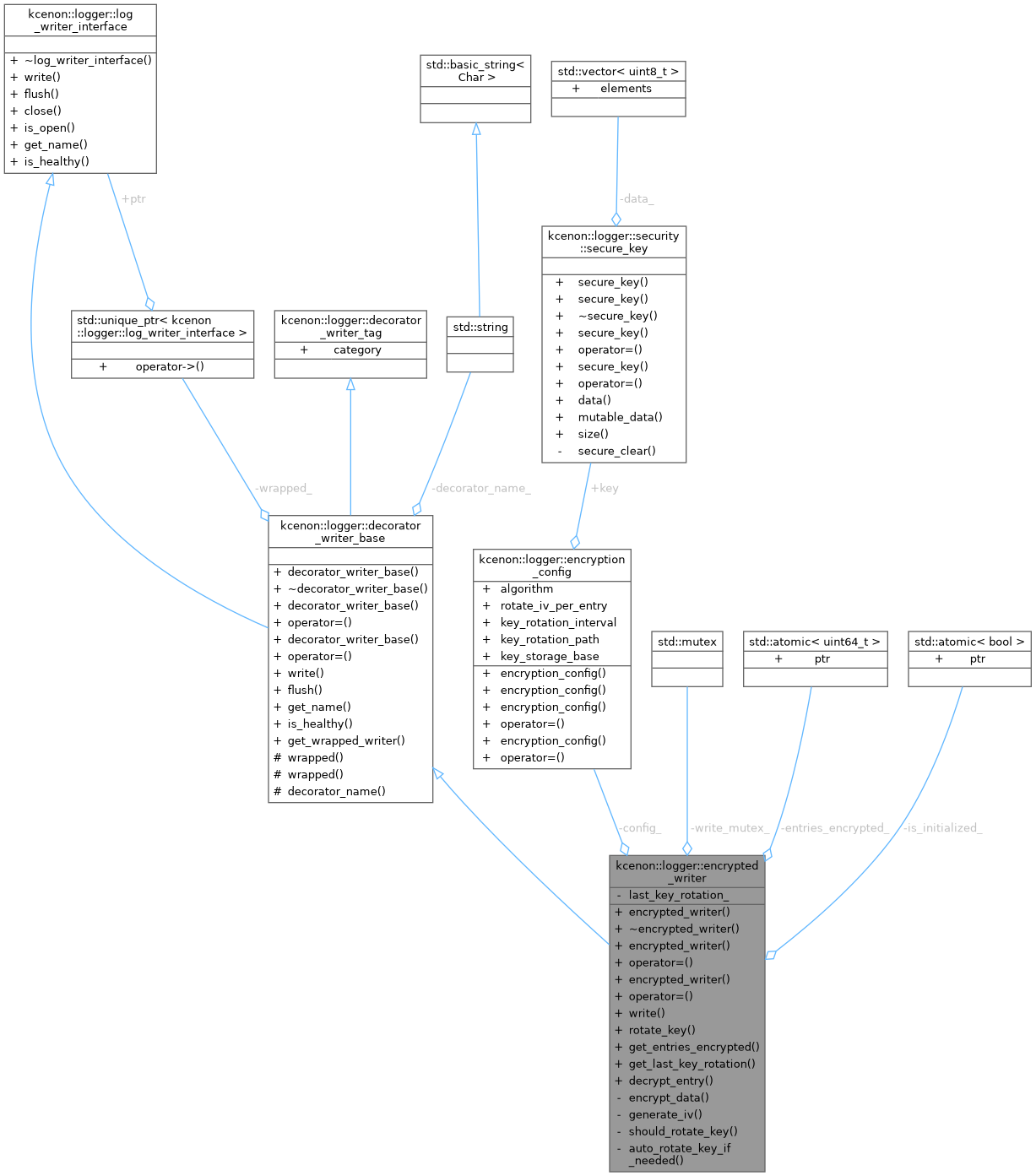
Decorator that encrypts log data before writing. More...
#include <encrypted_writer.h>
Public Member Functions | |
| encrypted_writer (std::unique_ptr< log_writer_interface > wrapped, encryption_config config) | |
| Construct encrypted writer with wrapped writer. | |
| ~encrypted_writer () override | |
| Destructor - securely cleans up key material. | |
| encrypted_writer (const encrypted_writer &)=delete | |
| encrypted_writer & | operator= (const encrypted_writer &)=delete |
| encrypted_writer (encrypted_writer &&)=delete | |
| encrypted_writer & | operator= (encrypted_writer &&)=delete |
| common::VoidResult | write (const log_entry &entry) override |
| Write encrypted log entry. | |
| common::VoidResult | rotate_key (security::secure_key new_key) |
| Rotate encryption key. | |
| uint64_t | get_entries_encrypted () const |
| Get encryption statistics. | |
| std::chrono::system_clock::time_point | get_last_key_rotation () const |
| Get time of last key rotation. | |
 Public Member Functions inherited from kcenon::logger::decorator_writer_base Public Member Functions inherited from kcenon::logger::decorator_writer_base | |
| decorator_writer_base (std::unique_ptr< log_writer_interface > wrapped, std::string_view decorator_name) | |
| Construct a decorator writer base. | |
| ~decorator_writer_base () override=default | |
| Virtual destructor for proper cleanup. | |
| decorator_writer_base (const decorator_writer_base &)=delete | |
| decorator_writer_base & | operator= (const decorator_writer_base &)=delete |
| decorator_writer_base (decorator_writer_base &&) noexcept=default | |
| decorator_writer_base & | operator= (decorator_writer_base &&) noexcept=default |
| common::VoidResult | flush () override |
| Flush the wrapped writer. | |
| std::string | get_name () const override |
| Get the name of this writer. | |
| bool | is_healthy () const override |
| Check if the writer is healthy. | |
| const log_writer_interface * | get_wrapped_writer () const noexcept |
| Get the wrapped writer (const version) | |
 Public Member Functions inherited from kcenon::logger::log_writer_interface Public Member Functions inherited from kcenon::logger::log_writer_interface | |
| virtual | ~log_writer_interface ()=default |
| virtual common::VoidResult | close () |
| Close the writer and release resources. | |
| virtual auto | is_open () const -> bool |
| Check if writer is open and ready. | |
Static Public Member Functions | |
| static result< std::string > | decrypt_entry (const std::vector< uint8_t > &encrypted_data, const security::secure_key &key) |
| Decrypt a single encrypted log entry. | |
Private Member Functions | |
| common::VoidResult | encrypt_data (const std::string &plaintext, std::vector< uint8_t > &output) |
| Encrypt plaintext using configured algorithm. | |
| common::VoidResult | generate_iv (uint8_t *iv) |
| Generate secure random IV. | |
| bool | should_rotate_key () const |
| Check if key rotation is needed. | |
| common::VoidResult | auto_rotate_key_if_needed () |
| Perform automatic key rotation if configured. | |
Private Attributes | |
| encryption_config | config_ |
| std::mutex | write_mutex_ |
| std::atomic< uint64_t > | entries_encrypted_ {0} |
| std::chrono::system_clock::time_point | last_key_rotation_ |
| std::atomic< bool > | is_initialized_ {false} |
Additional Inherited Members | |
 Static Public Attributes inherited from kcenon::logger::decorator_writer_tag Static Public Attributes inherited from kcenon::logger::decorator_writer_tag | |
| static constexpr writer_category | category = writer_category::decorator |
 Protected Member Functions inherited from kcenon::logger::decorator_writer_base Protected Member Functions inherited from kcenon::logger::decorator_writer_base | |
| log_writer_interface & | wrapped () noexcept |
| Access the wrapped writer (non-const) | |
| const log_writer_interface & | wrapped () const noexcept |
| Access the wrapped writer (const) | |
| const std::string & | decorator_name () const noexcept |
| Get the decorator name. | |
Detailed Description
Decorator that encrypts log data before writing.
Wraps any log_writer_interface and transparently encrypts all log data using AES-256-GCM before passing to the wrapped writer. Provides:
- Per-entry IV rotation for semantic security
- Authenticated encryption to prevent tampering
- Optional key rotation
- Secure key cleanup on destruction
Thread safety: Thread-safe when wrapped writer is thread-safe.
Category: Decorator (wraps another writer to add encryption)
- Since
- 1.3.0
- 1.4.0 Added decorator_writer_tag for category classification
- 4.0.0 Refactored to use decorator_writer_base
- Examples
- decorator_usage.cpp.
Definition at line 188 of file encrypted_writer.h.
Constructor & Destructor Documentation
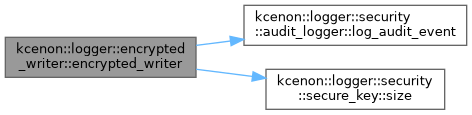
◆ encrypted_writer() [1/3]
|
explicit |
Construct encrypted writer with wrapped writer.
- Parameters
-
wrapped Writer to wrap (encrypts before delegating) config Encryption configuration (moved)
- Exceptions
-
std::invalid_argument if wrapped is null or key is invalid std::runtime_error if initialization fails
- Note
- The wrapped writer receives log entries with encrypted message field. For binary file output, wrap a file_writer: auto writer = std::make_unique<encrypted_writer>(std::make_unique<file_writer>("secure.log.enc"),std::move(config));
- Since
- 4.0.0
Definition at line 21 of file encrypted_writer.cpp.
References config_, kcenon::logger::security::audit_logger::encryption_key_loaded, is_initialized_, kcenon::logger::encryption_config::key, kcenon::logger::security::audit_logger::log_audit_event(), and kcenon::logger::security::secure_key::size().
◆ ~encrypted_writer()
|
override |
Destructor - securely cleans up key material.
Definition at line 57 of file encrypted_writer.cpp.
◆ encrypted_writer() [2/3]
|
delete |
◆ encrypted_writer() [3/3]
|
delete |
Member Function Documentation
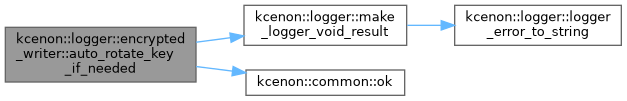
◆ auto_rotate_key_if_needed()
|
private |
Perform automatic key rotation if configured.
- Returns
- common::VoidResult Success or error code
Definition at line 452 of file encrypted_writer.cpp.
References kcenon::logger::make_logger_void_result(), and kcenon::common::ok().
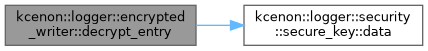
◆ decrypt_entry()
|
static |
Decrypt a single encrypted log entry.
- Parameters
-
encrypted_data Raw encrypted data including header key Decryption key
- Returns
- Result containing decrypted string or error
- Note
- Static utility method for log decryption tools
Definition at line 188 of file encrypted_writer.cpp.
References kcenon::logger::encrypted_log_header::algorithm, kcenon::logger::security::secure_key::data(), kcenon::logger::encrypted_log_header::encrypted_length, kcenon::logger::encrypted_log_header::iv, kcenon::logger::encrypted_log_header::magic, kcenon::logger::encrypted_log_header::original_length, kcenon::logger::encrypted_log_header::tag, and kcenon::logger::encrypted_log_header::version.
Referenced by kcenon::logger::log_decryptor::decrypt_file_streaming().

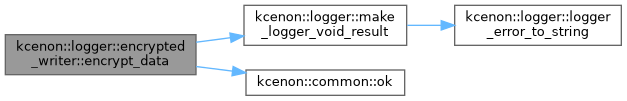
◆ encrypt_data()
|
private |
Encrypt plaintext using configured algorithm.
- Parameters
-
plaintext Data to encrypt output Buffer to receive encrypted data with header
- Returns
- common::VoidResult Success or error code
Definition at line 339 of file encrypted_writer.cpp.
References kcenon::logger::encrypted_log_header::algorithm, kcenon::logger::encrypted_log_header::encrypted_length, kcenon::logger::encrypted_log_header::iv, kcenon::logger::make_logger_void_result(), kcenon::common::ok(), kcenon::logger::encrypted_log_header::original_length, and kcenon::logger::encrypted_log_header::tag.
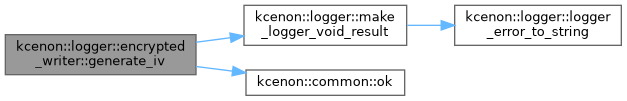
◆ generate_iv()
|
private |
Generate secure random IV.
- Parameters
-
iv Buffer to receive IV (must be 16 bytes)
- Returns
- common::VoidResult Success or error code
Definition at line 422 of file encrypted_writer.cpp.
References kcenon::logger::make_logger_void_result(), and kcenon::common::ok().
◆ get_entries_encrypted()
| uint64_t kcenon::logger::encrypted_writer::get_entries_encrypted | ( | ) | const |
Get encryption statistics.
- Returns
- Number of log entries encrypted since creation
Definition at line 180 of file encrypted_writer.cpp.
◆ get_last_key_rotation()
| std::chrono::system_clock::time_point kcenon::logger::encrypted_writer::get_last_key_rotation | ( | ) | const |
Get time of last key rotation.
- Returns
- Timestamp of last key rotation (or construction time)
Definition at line 184 of file encrypted_writer.cpp.
◆ operator=() [1/2]
|
delete |
◆ operator=() [2/2]
|
delete |
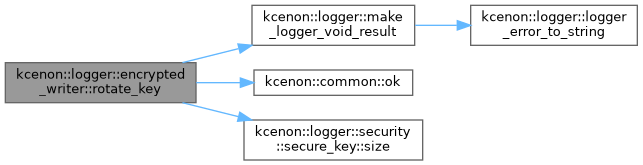
◆ rotate_key()
| common::VoidResult kcenon::logger::encrypted_writer::rotate_key | ( | security::secure_key | new_key | ) |
Rotate encryption key.
- Parameters
-
new_key New key to use (moved)
- Returns
- common::VoidResult Success or error code
Safely rotates the encryption key:
- Validates new key
- Flushes pending writes
- Swaps key atomically
- Securely clears old key
- Optionally logs to audit log
Definition at line 140 of file encrypted_writer.cpp.
References kcenon::logger::make_logger_void_result(), kcenon::common::ok(), and kcenon::logger::security::secure_key::size().
◆ should_rotate_key()
|
private |
Check if key rotation is needed.
- Returns
- true if rotation interval has elapsed
Definition at line 439 of file encrypted_writer.cpp.
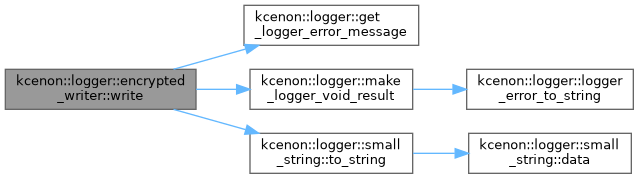
◆ write()
|
overridevirtual |
Write encrypted log entry.
- Parameters
-
entry The log entry to write
- Returns
- common::VoidResult Success or error code
- Since
- 3.5.0 Changed to use log_entry directly
Implements kcenon::logger::decorator_writer_base.
Definition at line 68 of file encrypted_writer.cpp.
References kcenon::logger::get_logger_error_message(), kcenon::logger::log_entry::level, kcenon::logger::log_entry::location, kcenon::logger::make_logger_void_result(), kcenon::logger::log_entry::message, kcenon::logger::log_entry::timestamp, and kcenon::logger::small_string< SSO_SIZE >::to_string().
Member Data Documentation
◆ config_
|
private |
Definition at line 315 of file encrypted_writer.h.
Referenced by encrypted_writer().
◆ entries_encrypted_
|
private |
Definition at line 318 of file encrypted_writer.h.
◆ is_initialized_
|
private |
◆ last_key_rotation_
|
private |
Definition at line 319 of file encrypted_writer.h.
◆ write_mutex_
|
mutableprivate |
Definition at line 316 of file encrypted_writer.h.
The documentation for this class was generated from the following files:
- include/kcenon/logger/writers/encrypted_writer.h
- src/impl/writers/encrypted_writer.cpp