Secure audit logging with tamper detection. More...
#include <audit_logger.h>
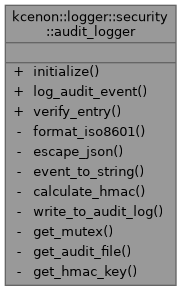
Public Types | |
| enum class | audit_event { logger_started , logger_stopped , writer_added , writer_removed , encryption_key_loaded , encryption_key_rotated , encryption_key_generated , permission_denied , path_traversal_attempt , insecure_permissions_detected , suspicious_activity , configuration_changed , authentication_success , authentication_failure , file_access_denied , file_access_granted } |
| Types of security-relevant events to audit. More... | |
Static Public Member Functions | |
| static void | initialize (const std::filesystem::path &audit_file, const secure_key *hmac_key=nullptr) |
| Initialize audit logger. | |
| static void | log_audit_event (audit_event event, const std::string &details, const std::map< std::string, std::string > &metadata={}) |
| Log an audit event. | |
| static bool | verify_entry (const std::string &json_entry, const std::string &signature) |
| Verify integrity of an audit log entry. | |
Static Private Member Functions | |
| static std::string | format_iso8601 (const std::chrono::system_clock::time_point &tp) |
| Format timestamp as ISO8601 string. | |
| static std::string | escape_json (const std::string &str) |
| Escape JSON special characters. | |
| static std::string | event_to_string (audit_event event) |
| Convert audit event to string. | |
| static std::string | calculate_hmac (const std::string &message, const secure_key &key) |
| Calculate HMAC signature. | |
| static void | write_to_audit_log (const std::string &json_entry, const std::string &signature) |
| Write entry to audit log file. | |
| static std::mutex & | get_mutex () |
| static std::filesystem::path & | get_audit_file () |
| static std::unique_ptr< secure_key > & | get_hmac_key () |
Detailed Description
Secure audit logging with tamper detection.
Features:
- JSON-formatted audit entries
- HMAC signatures for tamper detection
- Thread-safe logging
- Configurable audit file location
Definition at line 44 of file audit_logger.h.
Member Enumeration Documentation
◆ audit_event
|
strong |
Types of security-relevant events to audit.
Definition at line 50 of file audit_logger.h.
Member Function Documentation
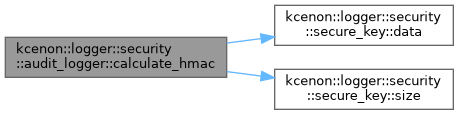
◆ calculate_hmac()
|
inlinestaticprivate |
Calculate HMAC signature.
- Parameters
-
message Message to sign key HMAC key
- Returns
- Hex-encoded signature
Definition at line 271 of file audit_logger.h.
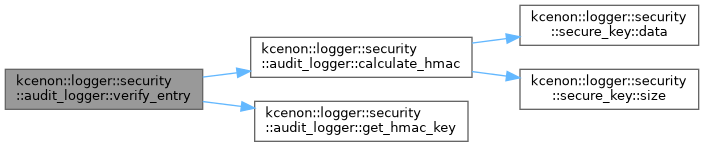
References kcenon::logger::security::secure_key::data(), and kcenon::logger::security::secure_key::size().
Referenced by verify_entry().
◆ escape_json()
|
inlinestaticprivate |
Escape JSON special characters.
Definition at line 200 of file audit_logger.h.
◆ event_to_string()
|
inlinestaticprivate |
Convert audit event to string.
Definition at line 226 of file audit_logger.h.
References authentication_failure, authentication_success, configuration_changed, encryption_key_generated, encryption_key_loaded, encryption_key_rotated, file_access_denied, file_access_granted, insecure_permissions_detected, logger_started, logger_stopped, path_traversal_attempt, permission_denied, suspicious_activity, writer_added, and writer_removed.
◆ format_iso8601()
|
inlinestaticprivate |
Format timestamp as ISO8601 string.
Definition at line 181 of file audit_logger.h.
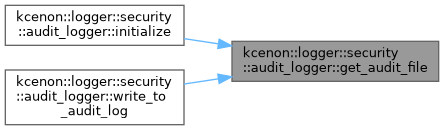
◆ get_audit_file()
|
inlinestaticprivate |
Definition at line 381 of file audit_logger.h.
Referenced by initialize(), and write_to_audit_log().
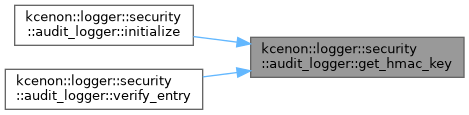
◆ get_hmac_key()
|
inlinestaticprivate |
Definition at line 386 of file audit_logger.h.
Referenced by initialize(), and verify_entry().
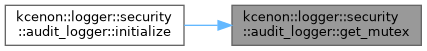
◆ get_mutex()
|
inlinestaticprivate |
Definition at line 376 of file audit_logger.h.
Referenced by initialize().
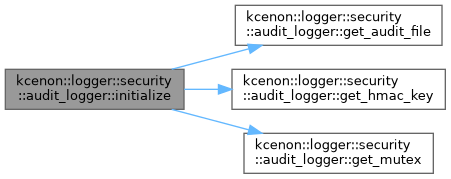
◆ initialize()
|
inlinestatic |
Initialize audit logger.
- Parameters
-
audit_file Path to audit log file hmac_key HMAC key for tamper detection (optional)
Definition at line 74 of file audit_logger.h.
References get_audit_file(), get_hmac_key(), and get_mutex().
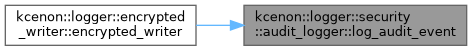
◆ log_audit_event()
|
inlinestatic |
Log an audit event.
- Parameters
-
event Event type details Event details metadata Additional metadata (key-value pairs)
Definition at line 110 of file audit_logger.h.
Referenced by kcenon::logger::encrypted_writer::encrypted_writer().
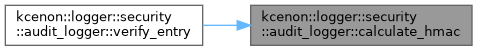
◆ verify_entry()
|
inlinestatic |
Verify integrity of an audit log entry.
- Parameters
-
json_entry JSON audit entry signature HMAC signature
- Returns
- true if signature is valid, false otherwise
Definition at line 165 of file audit_logger.h.
References calculate_hmac(), and get_hmac_key().
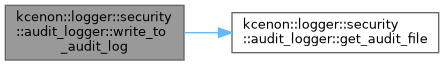
◆ write_to_audit_log()
|
inlinestaticprivate |
Write entry to audit log file.
- Parameters
-
json_entry JSON audit entry signature HMAC signature (optional)
Definition at line 352 of file audit_logger.h.
References get_audit_file().
The documentation for this class was generated from the following file:
- include/kcenon/logger/security/audit_logger.h