Secure storage and retrieval of encryption keys. More...
#include <secure_key_storage.h>
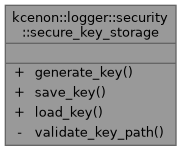
Static Public Member Functions | |
| static result< secure_key > | generate_key (size_t size=32) |
| Generate a secure random key. | |
| static common::VoidResult | save_key (const secure_key &key, const std::filesystem::path &path, const std::filesystem::path &allowed_base="/var/log/keys") |
| Save key to file with secure permissions. | |
| static result< secure_key > | load_key (const std::filesystem::path &path, size_t expected_size=32, const std::filesystem::path &allowed_base="/var/log/keys") |
| Load key from file with permission verification. | |
Static Private Member Functions | |
| static common::VoidResult | validate_key_path (const std::filesystem::path &path, const std::filesystem::path &allowed_base) |
| Validate key file path (prevent path traversal) | |
Detailed Description
Secure storage and retrieval of encryption keys.
Security features:
- File permission verification (0600)
- Path traversal prevention
- Secure random generation
- Memory cleanup after use
Definition at line 141 of file secure_key_storage.h.
Member Function Documentation
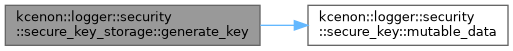
◆ generate_key()
|
inlinestatic |
Generate a secure random key.
- Parameters
-
size Key size in bytes (default: 32 for AES-256)
- Returns
- Result containing the generated key or error
Definition at line 148 of file secure_key_storage.h.
References kcenon::logger::encryption_failed, kcenon::logger::security::secure_key::mutable_data(), and kcenon::logger::size.
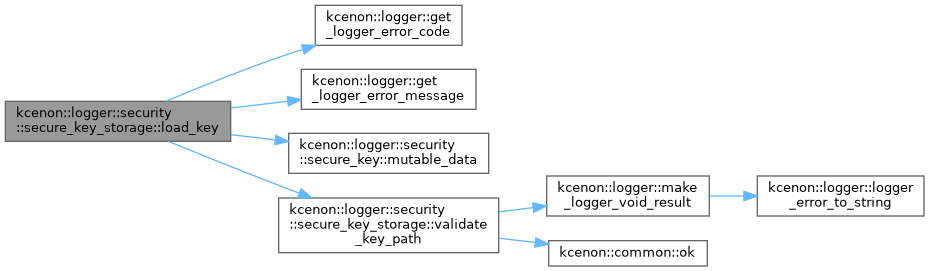
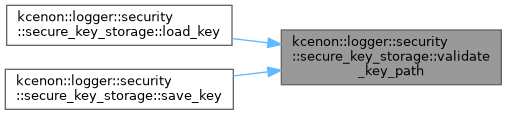
◆ load_key()
|
inlinestatic |
Load key from file with permission verification.
- Parameters
-
path File path expected_size Expected key size (default: 32 for AES-256) allowed_base Base directory for key storage
- Returns
- Result containing the loaded key or error
Definition at line 250 of file secure_key_storage.h.
References kcenon::logger::file_open_failed, kcenon::logger::file_permission_denied, kcenon::logger::file_read_failed, kcenon::logger::get_logger_error_code(), kcenon::logger::get_logger_error_message(), kcenon::logger::insecure_permissions, kcenon::logger::invalid_key_size, kcenon::logger::security::secure_key::mutable_data(), and validate_key_path().
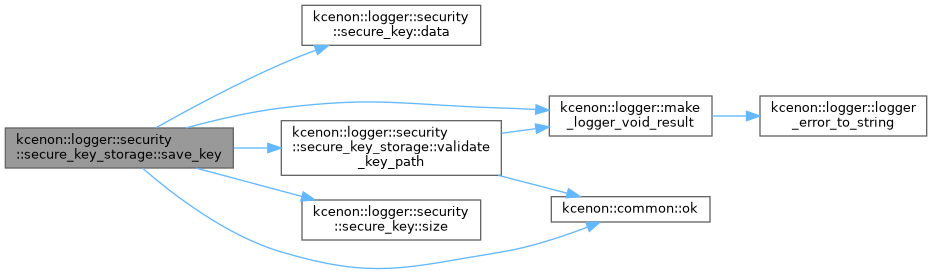
◆ save_key()
|
inlinestatic |
Save key to file with secure permissions.
- Parameters
-
key The key to save path File path (must be in allowed directory) allowed_base Base directory for key storage
- Returns
- Success or error
Definition at line 176 of file secure_key_storage.h.
References kcenon::logger::security::secure_key::data(), kcenon::logger::file_permission_denied, kcenon::logger::file_write_failed, kcenon::logger::make_logger_void_result(), kcenon::common::ok(), kcenon::logger::security::secure_key::size(), and validate_key_path().
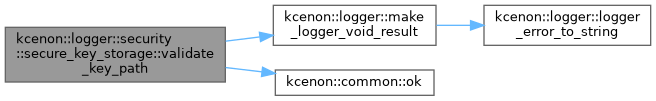
◆ validate_key_path()
|
inlinestaticprivate |
Validate key file path (prevent path traversal)
- Parameters
-
path Path to validate allowed_base Base directory that path must be within
- Returns
- Success or error
Definition at line 334 of file secure_key_storage.h.
References kcenon::logger::make_logger_void_result(), kcenon::common::ok(), and kcenon::logger::path_traversal_detected.
Referenced by load_key(), and save_key().
The documentation for this class was generated from the following file:
- include/kcenon/logger/security/secure_key_storage.h