Configuration for TLS/SSL connections. More...
#include <common_defs.h>
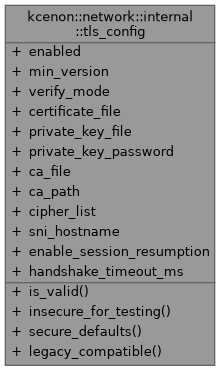
Public Member Functions | |
| auto | is_valid () const -> bool |
| Validates the TLS configuration. | |
Static Public Member Functions | |
| static auto | insecure_for_testing () -> tls_config |
| Creates a default insecure configuration (testing only) | |
| static auto | secure_defaults () -> tls_config |
| Creates a secure default configuration. | |
| static auto | legacy_compatible () -> tls_config |
| Creates a backwards-compatible configuration (TLS 1.2+) | |
Public Attributes | |
| bool | enabled = false |
| Enable TLS/SSL for this connection (default: false) | |
| tls_version | min_version = tls_version::tls_1_3 |
| Minimum TLS version to accept (default: TLS 1.3) Note: TLS 1.3 is enforced by default to prevent downgrade attacks (TICKET-009) | |
| certificate_verification | verify_mode = certificate_verification::verify_peer |
| Certificate verification mode (default: verify_peer) | |
| std::optional< std::string > | certificate_file |
| Path to server certificate file (PEM format) Required for servers when TLS is enabled. | |
| std::optional< std::string > | private_key_file |
| Path to server private key file (PEM format) Required for servers when TLS is enabled. | |
| std::optional< std::string > | private_key_password |
| Password for encrypted private key (if applicable) | |
| std::optional< std::string > | ca_file |
| Path to CA certificate file for verification (PEM format) Required when verify_mode != none. | |
| std::optional< std::string > | ca_path |
| Path to directory containing CA certificates. | |
| std::optional< std::string > | cipher_list |
| Cipher suite list (OpenSSL format) Default: Use strong ciphers (TLS 1.2+) Example: "ECDHE-RSA-AES256-GCM-SHA384:ECDHE-RSA-AES128-GCM-SHA256". | |
| std::optional< std::string > | sni_hostname |
| Server Name Indication (SNI) hostname for clients Used for virtual hosting and certificate selection. | |
| bool | enable_session_resumption = true |
| Enable session resumption for performance. | |
| std::size_t | handshake_timeout_ms = 10000 |
| Timeout for TLS handshake in milliseconds. | |
Detailed Description
Configuration for TLS/SSL connections.
This structure provides all necessary configuration for establishing secure TLS connections using ASIO SSL support.
Example Usage (Server)
Example Usage (Client)
Security Notes
- Always use TLS 1.2 or 1.3 in production
- Always verify peer certificates in production
- Protect private key files with appropriate file permissions
- Use strong cipher suites (configured via cipher_list)
Definition at line 163 of file common_defs.h.
Member Function Documentation
◆ insecure_for_testing()
|
inlinestaticnodiscard |
Creates a default insecure configuration (testing only)
- Returns
- TLS config with verification disabled
WARNING: This configuration is INSECURE and should only be used for development and testing. Never use in production!
Definition at line 239 of file common_defs.h.
References config, and kcenon::network::internal::none.
◆ is_valid()
|
inlinenodiscard |
Validates the TLS configuration.
- Returns
- true if configuration is valid, false otherwise
Checks that required files are specified for the chosen mode.
Definition at line 213 of file common_defs.h.
References ca_file, ca_path, enabled, kcenon::network::internal::none, and verify_mode.
◆ legacy_compatible()
|
inlinestaticnodiscard |
Creates a backwards-compatible configuration (TLS 1.2+)
- Returns
- TLS config allowing TLS 1.2 for legacy client compatibility
WARNING: This allows TLS 1.2 which may be vulnerable to downgrade attacks. Use only when TLS 1.3 is not supported by all clients.
Definition at line 269 of file common_defs.h.
References config, kcenon::network::internal::tls_1_2, and kcenon::network::internal::verify_peer.
◆ secure_defaults()
|
inlinestaticnodiscard |
Creates a secure default configuration.
- Returns
- TLS config with secure defaults (TLS 1.3 minimum)
You must still set certificate/key files and CA certificates. Uses TLS 1.3 by default to prevent protocol downgrade attacks.
Definition at line 253 of file common_defs.h.
References config, kcenon::network::internal::tls_1_3, and kcenon::network::internal::verify_peer.
Member Data Documentation
◆ ca_file
| std::optional<std::string> kcenon::network::internal::tls_config::ca_file |
Path to CA certificate file for verification (PEM format) Required when verify_mode != none.
Definition at line 187 of file common_defs.h.
Referenced by is_valid().
◆ ca_path
| std::optional<std::string> kcenon::network::internal::tls_config::ca_path |
Path to directory containing CA certificates.
Definition at line 190 of file common_defs.h.
Referenced by is_valid().
◆ certificate_file
| std::optional<std::string> kcenon::network::internal::tls_config::certificate_file |
Path to server certificate file (PEM format) Required for servers when TLS is enabled.
Definition at line 176 of file common_defs.h.
◆ cipher_list
| std::optional<std::string> kcenon::network::internal::tls_config::cipher_list |
Cipher suite list (OpenSSL format) Default: Use strong ciphers (TLS 1.2+) Example: "ECDHE-RSA-AES256-GCM-SHA384:ECDHE-RSA-AES128-GCM-SHA256".
Definition at line 195 of file common_defs.h.
◆ enable_session_resumption
| bool kcenon::network::internal::tls_config::enable_session_resumption = true |
Enable session resumption for performance.
Definition at line 202 of file common_defs.h.
◆ enabled
| bool kcenon::network::internal::tls_config::enabled = false |
Enable TLS/SSL for this connection (default: false)
Definition at line 165 of file common_defs.h.
Referenced by is_valid().
◆ handshake_timeout_ms
| std::size_t kcenon::network::internal::tls_config::handshake_timeout_ms = 10000 |
Timeout for TLS handshake in milliseconds.
Definition at line 205 of file common_defs.h.
◆ min_version
| tls_version kcenon::network::internal::tls_config::min_version = tls_version::tls_1_3 |
Minimum TLS version to accept (default: TLS 1.3) Note: TLS 1.3 is enforced by default to prevent downgrade attacks (TICKET-009)
Definition at line 169 of file common_defs.h.
◆ private_key_file
| std::optional<std::string> kcenon::network::internal::tls_config::private_key_file |
Path to server private key file (PEM format) Required for servers when TLS is enabled.
Definition at line 180 of file common_defs.h.
◆ private_key_password
| std::optional<std::string> kcenon::network::internal::tls_config::private_key_password |
Password for encrypted private key (if applicable)
Definition at line 183 of file common_defs.h.
◆ sni_hostname
| std::optional<std::string> kcenon::network::internal::tls_config::sni_hostname |
Server Name Indication (SNI) hostname for clients Used for virtual hosting and certificate selection.
Definition at line 199 of file common_defs.h.
◆ verify_mode
| certificate_verification kcenon::network::internal::tls_config::verify_mode = certificate_verification::verify_peer |
Certificate verification mode (default: verify_peer)
Definition at line 172 of file common_defs.h.
Referenced by is_valid().
The documentation for this struct was generated from the following file:
- src/internal/utils/common_defs.h