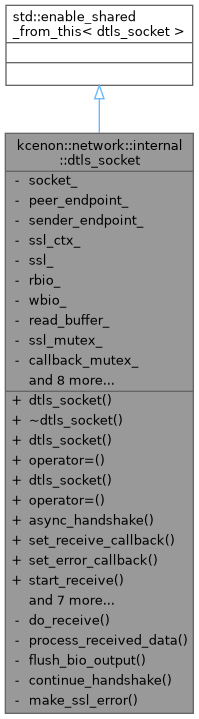
A wrapper around ASIO UDP socket with OpenSSL DTLS encryption. More...
#include <dtls_socket.h>
Public Types | |
| enum class | handshake_type { client , server } |
| Handshake type enumeration. More... | |
Public Member Functions | |
| dtls_socket (asio::ip::udp::socket socket, SSL_CTX *ssl_ctx) | |
Constructs a dtls_socket with an existing UDP socket. | |
| ~dtls_socket () | |
| Destructor. Cleans up OpenSSL resources. | |
| dtls_socket (const dtls_socket &)=delete | |
| dtls_socket & | operator= (const dtls_socket &)=delete |
| dtls_socket (dtls_socket &&)=delete | |
| dtls_socket & | operator= (dtls_socket &&)=delete |
| auto | async_handshake (handshake_type type, std::function< void(std::error_code)> handler) -> void |
| Performs asynchronous DTLS handshake. | |
| auto | set_receive_callback (std::function< void(const std::vector< uint8_t > &, const asio::ip::udp::endpoint &)> callback) -> void |
| Sets a callback to receive decrypted inbound datagrams. | |
| auto | set_error_callback (std::function< void(std::error_code)> callback) -> void |
| Sets a callback to handle socket errors. | |
| auto | start_receive () -> void |
| Begins the continuous asynchronous receive loop. | |
| auto | stop_receive () -> void |
| Stops the receive loop. | |
| auto | async_send (std::vector< uint8_t > &&data, std::function< void(std::error_code, std::size_t)> handler) -> void |
| Initiates an asynchronous encrypted send. | |
| auto | async_send_to (std::vector< uint8_t > &&data, const asio::ip::udp::endpoint &endpoint, std::function< void(std::error_code, std::size_t)> handler) -> void |
| Initiates an asynchronous encrypted send to a specific endpoint. | |
| auto | set_peer_endpoint (const asio::ip::udp::endpoint &endpoint) -> void |
| Sets the peer endpoint for connected mode. | |
| auto | peer_endpoint () const -> asio::ip::udp::endpoint |
| Returns the peer endpoint. | |
| auto | socket () -> asio::ip::udp::socket & |
| Provides direct access to the underlying UDP socket. | |
| auto | is_handshake_complete () const -> bool |
| Checks if the DTLS handshake is complete. | |
Private Member Functions | |
| auto | do_receive () -> void |
| Internal function to handle the receive logic. | |
| auto | process_received_data (const std::vector< uint8_t > &data, const asio::ip::udp::endpoint &sender) -> void |
| Processes received encrypted data through DTLS. | |
| auto | flush_bio_output () -> void |
| Flushes pending DTLS output to the network. | |
| auto | continue_handshake () -> void |
| Continues the handshake process. | |
| auto | make_ssl_error () const -> std::error_code |
| Creates an OpenSSL error code from the current error state. | |
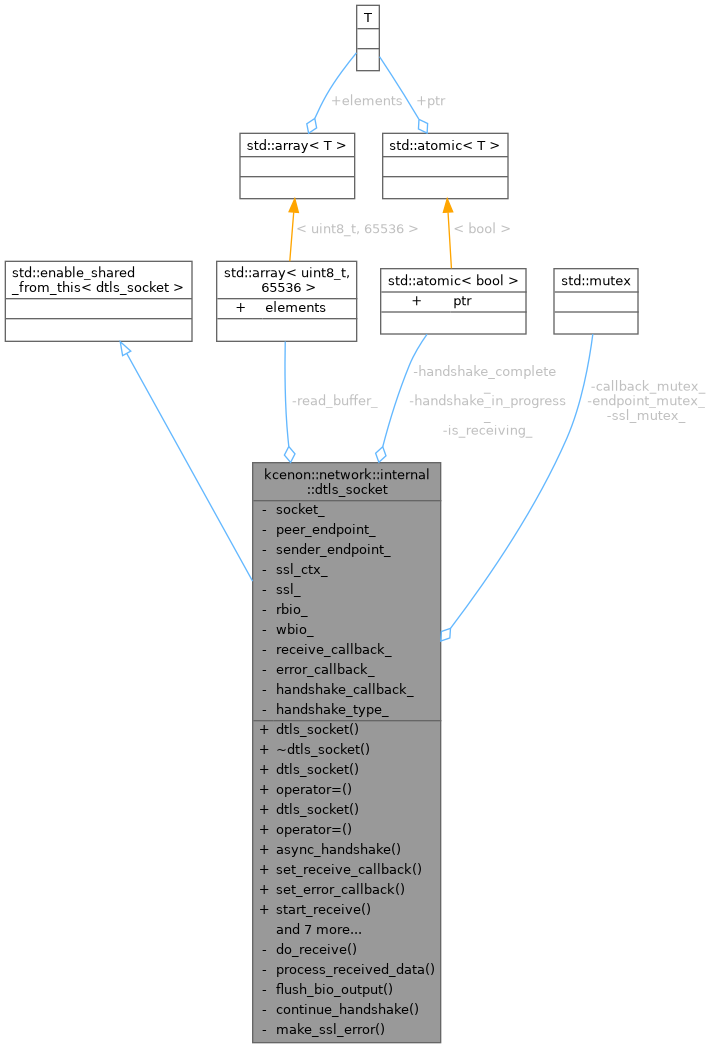
Private Attributes | |
| asio::ip::udp::socket | socket_ |
| asio::ip::udp::endpoint | peer_endpoint_ |
| asio::ip::udp::endpoint | sender_endpoint_ |
| SSL_CTX * | ssl_ctx_ |
| SSL * | ssl_ |
| BIO * | rbio_ |
| BIO * | wbio_ |
| std::array< uint8_t, 65536 > | read_buffer_ |
| std::mutex | ssl_mutex_ |
| std::mutex | callback_mutex_ |
| std::mutex | endpoint_mutex_ |
| std::function< void(const std::vector< uint8_t > &, const asio::ip::udp::endpoint &)> | receive_callback_ |
| std::function< void(std::error_code)> | error_callback_ |
| std::function< void(std::error_code)> | handshake_callback_ |
| std::atomic< bool > | is_receiving_ {false} |
| std::atomic< bool > | handshake_complete_ {false} |
| std::atomic< bool > | handshake_in_progress_ {false} |
| handshake_type | handshake_type_ {handshake_type::client} |
Detailed Description
A wrapper around ASIO UDP socket with OpenSSL DTLS encryption.
Key Features
- Provides DTLS (Datagram TLS) encryption over UDP transport.
- Uses OpenSSL's DTLS implementation with memory BIOs for async I/O.
- Exposes
set_receive_callback()to handle decrypted inbound datagrams andset_error_callback()for error handling. start_receive()begins an ongoing loop of receiving encrypted datagrams.async_send()encrypts and sends data to the configured peer.
Thread Safety
- All public methods are thread-safe. Callback registration is protected by callback_mutex_.
- ASIO operations are serialized through the io_context.
- OpenSSL operations are protected by ssl_mutex_.
- The provided callbacks will be invoked on an ASIO worker thread; ensure that your callback logic is thread-safe if it shares data.
DTLS Characteristics
- Provides confidentiality and integrity for UDP datagrams.
- Handles packet loss and reordering during handshake.
- Message boundaries are preserved (each receive is one datagram).
- Suitable for real-time applications requiring encryption.
Definition at line 48 of file dtls_socket.h.
Member Enumeration Documentation
◆ handshake_type
|
strong |
Handshake type enumeration.
| Enumerator | |
|---|---|
| client | Client-side handshake |
| server | Server-side handshake |
Definition at line 54 of file dtls_socket.h.
Constructor & Destructor Documentation
◆ dtls_socket() [1/3]
| kcenon::network::internal::dtls_socket::dtls_socket | ( | asio::ip::udp::socket | socket, |
| SSL_CTX * | ssl_ctx ) |
Constructs a dtls_socket with an existing UDP socket.
- Parameters
-
socket An asio::ip::udp::socketthat must be open.ssl_ctx The OpenSSL SSL_CTX configured for DTLS.
The socket should be connected (for client) or bound (for server) before calling handshake methods.
Definition at line 42 of file dtls_socket.cpp.
◆ ~dtls_socket()
| kcenon::network::internal::dtls_socket::~dtls_socket | ( | ) |
Destructor. Cleans up OpenSSL resources.
Definition at line 78 of file dtls_socket.cpp.
References ssl_, and stop_receive().
◆ dtls_socket() [2/3]
|
delete |
◆ dtls_socket() [3/3]
|
delete |
Member Function Documentation
◆ async_handshake()
| auto kcenon::network::internal::dtls_socket::async_handshake | ( | handshake_type | type, |
| std::function< void(std::error_code)> | handler ) -> void |
Performs asynchronous DTLS handshake.
- Parameters
-
type Handshake type (client or server) handler Completion handler with signature void(std::error_code)
Must be called before start_receive() or async_send(). The handshake involves multiple round-trips over UDP.
Definition at line 89 of file dtls_socket.cpp.
◆ async_send()
| auto kcenon::network::internal::dtls_socket::async_send | ( | std::vector< uint8_t > && | data, |
| std::function< void(std::error_code, std::size_t)> | handler ) -> void |
Initiates an asynchronous encrypted send.
- Parameters
-
data The plaintext data to encrypt and send (moved for efficiency). handler A completion handler with signature void(std::error_code, std::size_t)invoked upon completion.
The data is encrypted using DTLS before transmission.
- Note
- Data is moved (not copied) to avoid memory allocation overhead.
Definition at line 371 of file dtls_socket.cpp.
◆ async_send_to()
| auto kcenon::network::internal::dtls_socket::async_send_to | ( | std::vector< uint8_t > && | data, |
| const asio::ip::udp::endpoint & | endpoint, | ||
| std::function< void(std::error_code, std::size_t)> | handler ) -> void |
Initiates an asynchronous encrypted send to a specific endpoint.
- Parameters
-
data The plaintext data to encrypt and send (moved for efficiency). endpoint The target endpoint. handler A completion handler invoked upon completion.
Useful for server responding to different clients.
Definition at line 384 of file dtls_socket.cpp.
◆ continue_handshake()
|
private |
Continues the handshake process.
Definition at line 117 of file dtls_socket.cpp.
◆ do_receive()
|
private |
Internal function to handle the receive logic.
Definition at line 211 of file dtls_socket.cpp.
◆ flush_bio_output()
|
private |
Flushes pending DTLS output to the network.
Definition at line 330 of file dtls_socket.cpp.
◆ is_handshake_complete()
|
inline |
Checks if the DTLS handshake is complete.
- Returns
- true if handshake completed successfully.
Definition at line 177 of file dtls_socket.h.
References handshake_complete_.
◆ make_ssl_error()
|
private |
Creates an OpenSSL error code from the current error state.
- Returns
- std::error_code representing the SSL error.
Definition at line 472 of file dtls_socket.cpp.
◆ operator=() [1/2]
|
delete |
◆ operator=() [2/2]
|
delete |
◆ peer_endpoint()
| auto kcenon::network::internal::dtls_socket::peer_endpoint | ( | ) | const -> asio::ip::udp::endpoint |
Returns the peer endpoint.
- Returns
- The configured peer endpoint.
Definition at line 466 of file dtls_socket.cpp.
References endpoint_mutex_, and peer_endpoint_.
◆ process_received_data()
|
private |
Processes received encrypted data through DTLS.
- Parameters
-
data The encrypted datagram. sender The sender's endpoint.
Definition at line 258 of file dtls_socket.cpp.
◆ set_error_callback()
| auto kcenon::network::internal::dtls_socket::set_error_callback | ( | std::function< void(std::error_code)> | callback | ) | -> void |
Sets a callback to handle socket errors.
- Parameters
-
callback A function with signature void(std::error_code), invoked when any asynchronous operation fails.
If no callback is set, errors are not explicitly handled here.
Definition at line 190 of file dtls_socket.cpp.
◆ set_peer_endpoint()
| auto kcenon::network::internal::dtls_socket::set_peer_endpoint | ( | const asio::ip::udp::endpoint & | endpoint | ) | -> void |
Sets the peer endpoint for connected mode.
- Parameters
-
endpoint The peer's UDP endpoint.
Definition at line 460 of file dtls_socket.cpp.
◆ set_receive_callback()
| auto kcenon::network::internal::dtls_socket::set_receive_callback | ( | std::function< void(const std::vector< uint8_t > &, const asio::ip::udp::endpoint &)> | callback | ) | -> void |
Sets a callback to receive decrypted inbound datagrams.
- Parameters
-
callback A function with signature void(const std::vector<uint8_t>&, const asio::ip::udp::endpoint&), called whenever a datagram is successfully received and decrypted.
If no callback is set, received data is effectively discarded.
Definition at line 182 of file dtls_socket.cpp.
◆ socket()
|
inline |
Provides direct access to the underlying UDP socket.
- Returns
- A reference to the wrapped
asio::ip::udp::socket.
Definition at line 171 of file dtls_socket.h.
References socket_.
◆ start_receive()
| auto kcenon::network::internal::dtls_socket::start_receive | ( | ) | -> void |
Begins the continuous asynchronous receive loop.
Once called, the class repeatedly receives encrypted datagrams, decrypts them, and invokes the receive callback. If an error occurs, the error callback is triggered.
Definition at line 197 of file dtls_socket.cpp.
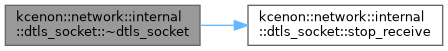
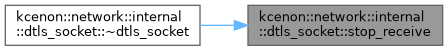
◆ stop_receive()
| auto kcenon::network::internal::dtls_socket::stop_receive | ( | ) | -> void |
Stops the receive loop.
Definition at line 206 of file dtls_socket.cpp.
Referenced by ~dtls_socket().
Member Data Documentation
◆ callback_mutex_
|
private |
Protects callback registration.
Definition at line 225 of file dtls_socket.h.
◆ endpoint_mutex_
|
private |
Protects endpoint access.
Definition at line 226 of file dtls_socket.h.
Referenced by peer_endpoint().
◆ error_callback_
|
private |
Error callback.
Definition at line 231 of file dtls_socket.h.
◆ handshake_callback_
|
private |
Handshake completion callback.
Definition at line 233 of file dtls_socket.h.
◆ handshake_complete_
|
private |
Handshake completed flag.
Definition at line 236 of file dtls_socket.h.
Referenced by is_handshake_complete().
◆ handshake_in_progress_
|
private |
◆ handshake_type_
|
private |
◆ is_receiving_
|
private |
◆ peer_endpoint_
|
private |
Peer endpoint for connected mode.
Definition at line 214 of file dtls_socket.h.
Referenced by peer_endpoint().
◆ rbio_
|
private |
◆ read_buffer_
|
private |
Buffer for receiving datagrams.
Definition at line 222 of file dtls_socket.h.
◆ receive_callback_
|
private |
Inbound data callback.
Definition at line 229 of file dtls_socket.h.
◆ sender_endpoint_
|
private |
Sender endpoint for receives.
Definition at line 215 of file dtls_socket.h.
◆ socket_
|
private |
◆ ssl_
|
private |
OpenSSL SSL object.
Definition at line 218 of file dtls_socket.h.
Referenced by dtls_socket(), and ~dtls_socket().
◆ ssl_ctx_
|
private |
OpenSSL context (not owned).
Definition at line 217 of file dtls_socket.h.
Referenced by dtls_socket().
◆ ssl_mutex_
|
private |
Protects SSL operations.
Definition at line 224 of file dtls_socket.h.
◆ wbio_
|
private |
The documentation for this class was generated from the following files:
- src/internal/tcp/dtls_socket.h
- src/internal/dtls_socket.cpp