Enterprise security framework with TLS, RBAC, audit logging, and threat detection. More...
#include <iostream>#include <string>#include <chrono>#include <memory>#include <vector>#include "database/database_manager.h"#include "database/security/secure_connection.h"#include "database/core/database_context.h"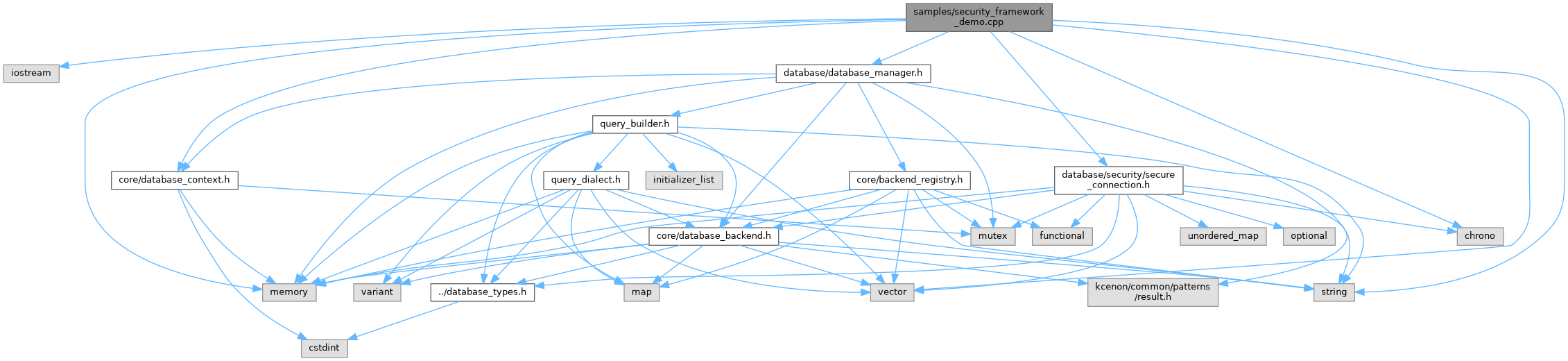
Go to the source code of this file.
Functions | |
| void | demonstrate_secure_connections () |
| void | demonstrate_credential_management () |
| void | demonstrate_rbac_system () |
| void | demonstrate_audit_logging (std::shared_ptr< security::audit_logger > audit_log) |
| void | demonstrate_threat_detection () |
| bool | detect_sql_injection (const std::string &query) |
| void | demonstrate_session_management () |
| int | main () |
Detailed Description
Enterprise security framework with TLS, RBAC, audit logging, and threat detection.
Definition in file security_framework_demo.cpp.
Function Documentation
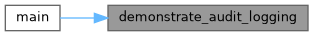
◆ demonstrate_audit_logging()
| void demonstrate_audit_logging | ( | std::shared_ptr< security::audit_logger > | audit_log | ) |
- Examples
- security_framework_demo.cpp.
Definition at line 204 of file security_framework_demo.cpp.
Referenced by main().
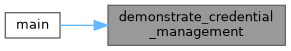
◆ demonstrate_credential_management()
| void demonstrate_credential_management | ( | ) |
- Examples
- security_framework_demo.cpp.
Definition at line 71 of file security_framework_demo.cpp.
References database::security::password.
Referenced by main().
◆ demonstrate_rbac_system()
| void demonstrate_rbac_system | ( | ) |
- Examples
- security_framework_demo.cpp.
Definition at line 123 of file security_framework_demo.cpp.
Referenced by main().
◆ demonstrate_secure_connections()
| void demonstrate_secure_connections | ( | ) |
- Examples
- security_framework_demo.cpp.
Definition at line 33 of file security_framework_demo.cpp.
Referenced by main().
◆ demonstrate_session_management()
| void demonstrate_session_management | ( | ) |
- Examples
- security_framework_demo.cpp.
Definition at line 374 of file security_framework_demo.cpp.
Referenced by main().
◆ demonstrate_threat_detection()
| void demonstrate_threat_detection | ( | ) |
- Examples
- security_framework_demo.cpp.
Definition at line 291 of file security_framework_demo.cpp.
References detect_sql_injection().
Referenced by main().

◆ detect_sql_injection()
| bool detect_sql_injection | ( | const std::string & | query | ) |
- Examples
- security_framework_demo.cpp.
Definition at line 347 of file security_framework_demo.cpp.
Referenced by demonstrate_threat_detection().

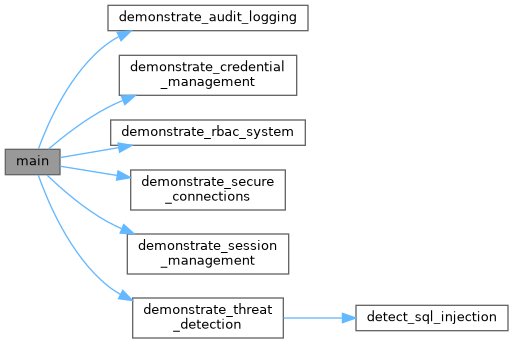
◆ main()
| int main | ( | ) |
Definition at line 407 of file security_framework_demo.cpp.
References demonstrate_audit_logging(), demonstrate_credential_management(), demonstrate_rbac_system(), demonstrate_secure_connections(), demonstrate_session_management(), and demonstrate_threat_detection().