#include <gtest/gtest.h>#include <memory>#include <chrono>#include <thread>#include <future>#include <vector>#include "database/database_manager.h"#include "database/database_types.h"#include "database/core/database_context.h"#include "database/orm/entity.h"#include "database/monitoring/performance_monitor.h"#include "database/security/secure_connection.h"#include "database/async/async_operations.h"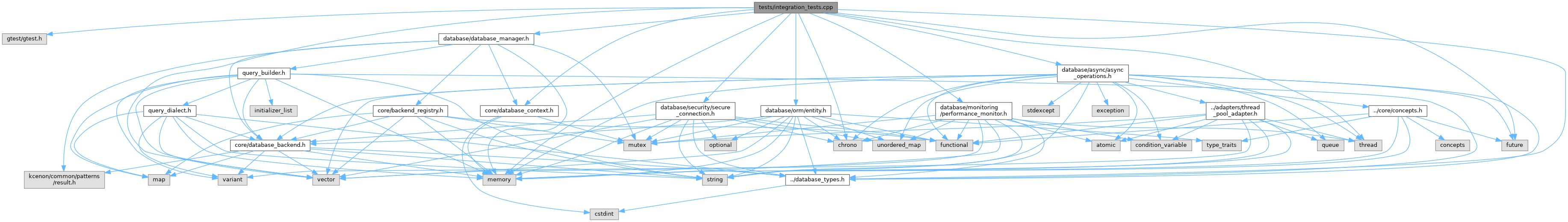
Go to the source code of this file.
Classes | |
| class | IntegrationTestUser |
| class | IntegrationTestBase |
| class | ORMSecurityIntegrationTest |
| class | PerformanceAsyncIntegrationTest |
| class | SecurityMonitoringIntegrationTest |
| class | FullSystemIntegrationTest |
| class | ErrorHandlingIntegrationTest |
| class | ConcurrentOperationsIntegrationTest |
Functions | |
| TEST_F (ORMSecurityIntegrationTest, SecureEntityOperations) | |
| TEST_F (PerformanceAsyncIntegrationTest, MonitoredAsyncOperations) | |
| TEST_F (SecurityMonitoringIntegrationTest, MonitoredSecurityEvents) | |
| TEST_F (FullSystemIntegrationTest, CompleteWorkflow) | |
| TEST_F (ErrorHandlingIntegrationTest, FailureRecoveryWorkflow) | |
| TEST_F (ConcurrentOperationsIntegrationTest, ConcurrentSecureOperations) | |
| int | main (int argc, char **argv) |
Function Documentation
◆ main()
| int main | ( | int | argc, |
| char ** | argv ) |
Definition at line 567 of file integration_tests.cpp.
◆ TEST_F() [1/6]
| TEST_F | ( | ConcurrentOperationsIntegrationTest | , |
| ConcurrentSecureOperations | ) |
Definition at line 481 of file integration_tests.cpp.
References database::monitoring::query_metrics::execution_time, database::security::has_permission(), database::monitoring::query_metrics::rows_affected, and database::monitoring::query_metrics::success.

◆ TEST_F() [2/6]
| TEST_F | ( | ErrorHandlingIntegrationTest | , |
| FailureRecoveryWorkflow | ) |
Definition at line 418 of file integration_tests.cpp.
References database::monitoring::query_metrics::execution_time, database::monitoring::query_metrics::rows_affected, and database::monitoring::query_metrics::success.
◆ TEST_F() [3/6]
| TEST_F | ( | FullSystemIntegrationTest | , |
| CompleteWorkflow | ) |
Definition at line 332 of file integration_tests.cpp.
References database::monitoring::query_metrics::execution_time, database::monitoring::query_metrics::rows_affected, and database::monitoring::query_metrics::success.
◆ TEST_F() [4/6]
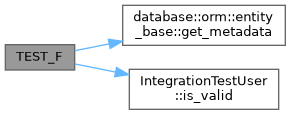
| TEST_F | ( | ORMSecurityIntegrationTest | , |
| SecureEntityOperations | ) |
Definition at line 160 of file integration_tests.cpp.
References database::orm::entity_base::get_metadata(), and IntegrationTestUser::is_valid().
◆ TEST_F() [5/6]
| TEST_F | ( | PerformanceAsyncIntegrationTest | , |
| MonitoredAsyncOperations | ) |
Definition at line 205 of file integration_tests.cpp.
References database::monitoring::query_metrics::execution_time, database::monitoring::query_metrics::rows_affected, and database::monitoring::query_metrics::success.
◆ TEST_F() [6/6]
| TEST_F | ( | SecurityMonitoringIntegrationTest | , |
| MonitoredSecurityEvents | ) |
Definition at line 259 of file integration_tests.cpp.
References database::monitoring::query_metrics::execution_time, database::security::has_permission(), database::monitoring::query_metrics::rows_affected, and database::monitoring::query_metrics::success.
