#include <gtest/gtest.h>#include <memory>#include <string>#include <sstream>#include <vector>#include <regex>#include "database/backends/sqlite_backend.h"#include "database/core/database_backend.h"#include "database/query_builder.h"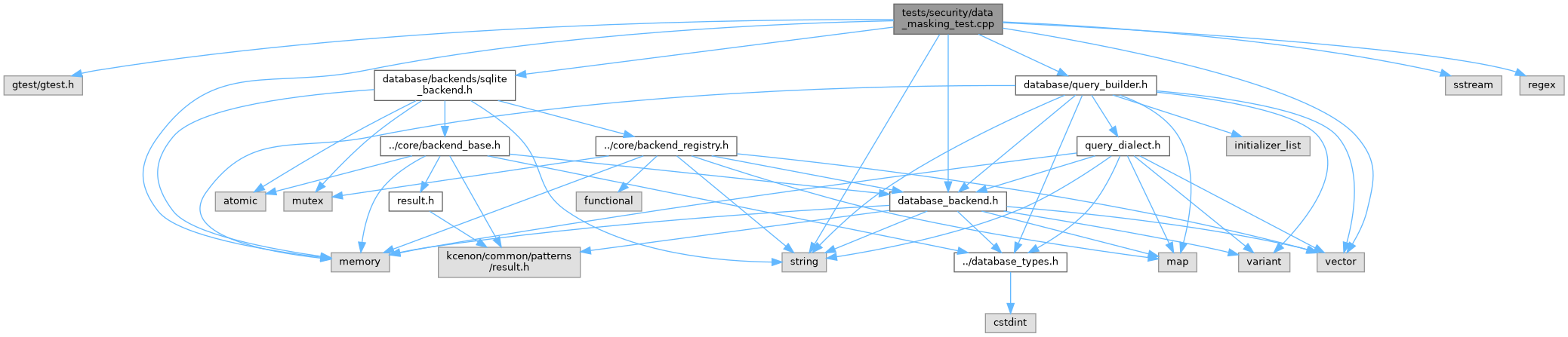
Go to the source code of this file.
Classes | |
| class | DataMaskingTest |
| Test fixture for data masking security tests. More... | |
Functions | |
| TEST_F (DataMaskingTest, QueryResultsNotLeakedInExceptions) | |
| Tests that query results don't appear in exception messages. | |
| TEST_F (DataMaskingTest, DatabaseErrorsNotLeakData) | |
| Tests that database-level errors don't expose data. | |
| TEST_F (DataMaskingTest, ResultDebugOutputMasked) | |
| Tests that debug representations of results mask sensitive fields. | |
| TEST_F (DataMaskingTest, QueryBuilderDoesNotLogSensitiveData) | |
| Tests that query builder operations don't log sensitive values. | |
| TEST_F (DataMaskingTest, SensitiveColumnNamePatterns) | |
| Documents patterns that should be treated as sensitive. | |
| TEST_F (DataMaskingTest, PIINotInStackTraces) | |
| Tests that PII doesn't appear in stack traces. | |
| TEST_F (DataMaskingTest, LargeDataSetDoesNotLeakOnError) | |
| Tests that large result sets don't leak on error. | |
| TEST_F (DataMaskingTest, SensitiveDataClearedFromResult) | |
| Tests that sensitive data is clearable from result objects. | |
| TEST_F (DataMaskingTest, StringValueSecureClearing) | |
| Documents the need for secure string clearing. | |
| TEST_F (DataMaskingTest, DebugLogLevelDoesNotExposeSecrets) | |
| Tests that even debug-level logging masks sensitive data. | |
| TEST_F (DataMaskingTest, ErrorLogMasksSensitiveContext) | |
| Tests that error logs mask sensitive context. | |
| TEST_F (DataMaskingTest, CreditCardMaskingFormat) | |
| Documents expected credit card masking format. | |
| TEST_F (DataMaskingTest, SSNMaskingFormat) | |
| Documents expected SSN masking format. | |
Function Documentation
◆ TEST_F() [1/13]
| TEST_F | ( | DataMaskingTest | , |
| CreditCardMaskingFormat | ) |
Documents expected credit card masking format.
- Test
- CreditCardMaskingFormat
Definition at line 429 of file data_masking_test.cpp.
◆ TEST_F() [2/13]
| TEST_F | ( | DataMaskingTest | , |
| DatabaseErrorsNotLeakData | ) |
Tests that database-level errors don't expose data.
- Test
- DatabaseErrorsNotLeakData
Definition at line 132 of file data_masking_test.cpp.
◆ TEST_F() [3/13]
| TEST_F | ( | DataMaskingTest | , |
| DebugLogLevelDoesNotExposeSecrets | ) |
Tests that even debug-level logging masks sensitive data.
- Test
- DebugLogLevelDoesNotExposeSecrets
Definition at line 390 of file data_masking_test.cpp.
◆ TEST_F() [4/13]
| TEST_F | ( | DataMaskingTest | , |
| ErrorLogMasksSensitiveContext | ) |
Tests that error logs mask sensitive context.
- Test
- ErrorLogMasksSensitiveContext
Definition at line 401 of file data_masking_test.cpp.
◆ TEST_F() [5/13]
| TEST_F | ( | DataMaskingTest | , |
| LargeDataSetDoesNotLeakOnError | ) |
Tests that large result sets don't leak on error.
- Test
- LargeDataSetDoesNotLeakOnError
Definition at line 308 of file data_masking_test.cpp.
References ASSERT_TRUE.
◆ TEST_F() [6/13]
| TEST_F | ( | DataMaskingTest | , |
| PIINotInStackTraces | ) |
Tests that PII doesn't appear in stack traces.
- Test
- PIINotInStackTraces
Definition at line 285 of file data_masking_test.cpp.
References ASSERT_FALSE, and ASSERT_TRUE.
◆ TEST_F() [7/13]
| TEST_F | ( | DataMaskingTest | , |
| QueryBuilderDoesNotLogSensitiveData | ) |
Tests that query builder operations don't log sensitive values.
- Test
- QueryBuilderDoesNotLogSensitiveData
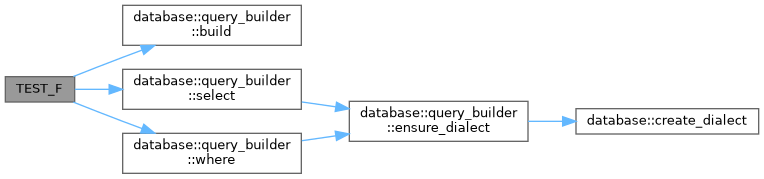
Definition at line 214 of file data_masking_test.cpp.
References database::query_builder::build(), database::query_builder::select(), and database::query_builder::where().
◆ TEST_F() [8/13]
| TEST_F | ( | DataMaskingTest | , |
| QueryResultsNotLeakedInExceptions | ) |
Tests that query results don't appear in exception messages.
- Test
- QueryResultsNotLeakedInExceptions
When an error occurs after fetching sensitive data, the exception message should not contain the data values.
Definition at line 105 of file data_masking_test.cpp.
References ASSERT_FALSE, and ASSERT_TRUE.
◆ TEST_F() [9/13]
| TEST_F | ( | DataMaskingTest | , |
| ResultDebugOutputMasked | ) |
Tests that debug representations of results mask sensitive fields.
- Test
- ResultDebugOutputMasked
Definition at line 160 of file data_masking_test.cpp.
References ASSERT_FALSE, and ASSERT_TRUE.
◆ TEST_F() [10/13]
| TEST_F | ( | DataMaskingTest | , |
| SensitiveColumnNamePatterns | ) |
Documents patterns that should be treated as sensitive.
- Test
- SensitiveColumnNamePatterns
These column name patterns should trigger masking in debug/logging output.
Definition at line 246 of file data_masking_test.cpp.
◆ TEST_F() [11/13]
| TEST_F | ( | DataMaskingTest | , |
| SensitiveDataClearedFromResult | ) |
Tests that sensitive data is clearable from result objects.
- Test
- SensitiveDataClearedFromResult
Definition at line 340 of file data_masking_test.cpp.
References ASSERT_FALSE, and ASSERT_TRUE.
◆ TEST_F() [12/13]
| TEST_F | ( | DataMaskingTest | , |
| SSNMaskingFormat | ) |
Documents expected SSN masking format.
- Test
- SSNMaskingFormat
Definition at line 444 of file data_masking_test.cpp.
◆ TEST_F() [13/13]
| TEST_F | ( | DataMaskingTest | , |
| StringValueSecureClearing | ) |
Documents the need for secure string clearing.
- Test
- StringValueSecureClearing
Definition at line 367 of file data_masking_test.cpp.