Manages encrypted credential storage and retrieval. More...
#include <secure_connection.h>
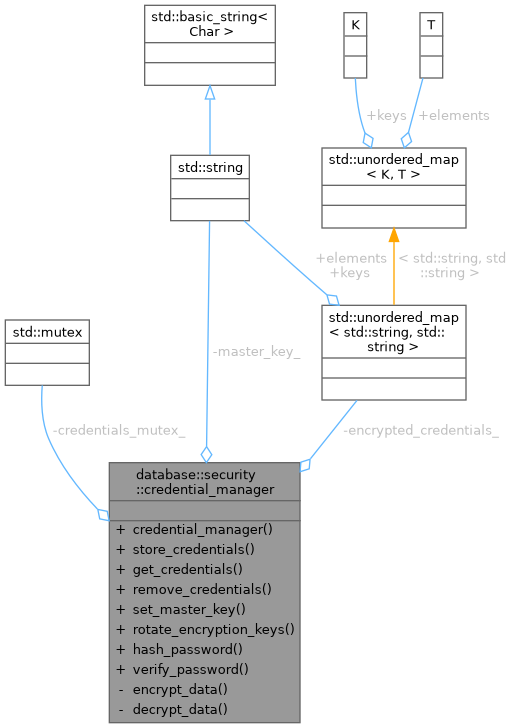
Public Member Functions | |
| credential_manager ()=default | |
| Default constructor - used by database_context. | |
| bool | store_credentials (const std::string &connection_id, const security_credentials &credentials) |
| std::optional< security_credentials > | get_credentials (const std::string &connection_id) const |
| bool | remove_credentials (const std::string &connection_id) |
| void | set_master_key (const std::string &key) |
| bool | rotate_encryption_keys () |
| std::string | hash_password (const std::string &password) const |
| bool | verify_password (const std::string &password, const std::string &hash) const |
Private Member Functions | |
| std::string | encrypt_data (const std::string &data) const |
| std::string | decrypt_data (const std::string &encrypted_data) const |
Private Attributes | |
| std::mutex | credentials_mutex_ |
| std::unordered_map< std::string, std::string > | encrypted_credentials_ |
| std::string | master_key_ |
Detailed Description
Manages encrypted credential storage and retrieval.
- Note
- This class uses dependency injection pattern. Access via database_context::get_credential_manager() (Sprint 3, Task 3.3).
Example:
Definition at line 99 of file secure_connection.h.
Constructor & Destructor Documentation
◆ credential_manager()
|
default |
Default constructor - used by database_context.
Member Function Documentation
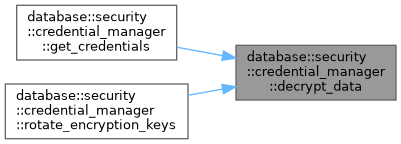
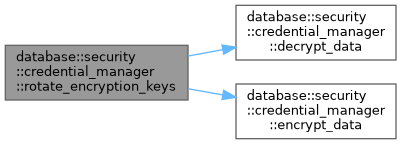
◆ decrypt_data()
|
private |
Definition at line 352 of file secure_connection.cpp.
References master_key_.
Referenced by get_credentials(), and rotate_encryption_keys().
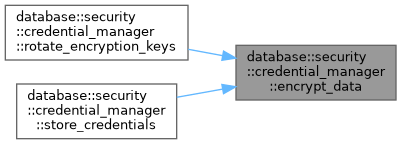
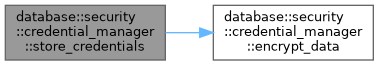
◆ encrypt_data()
|
private |
Definition at line 282 of file secure_connection.cpp.
References master_key_.
Referenced by rotate_encryption_keys(), and store_credentials().
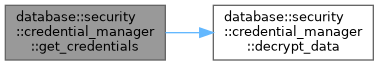
◆ get_credentials()
| std::optional< security_credentials > database::security::credential_manager::get_credentials | ( | const std::string & | connection_id | ) | const |
Definition at line 51 of file secure_connection.cpp.
References database::security::security_credentials::auth_method, database::security::security_credentials::ca_cert_path, database::security::security_credentials::certificate_path, credentials_mutex_, decrypt_data(), encrypted_credentials_, database::security::security_credentials::encryption, database::security::security_credentials::password_hash, database::security::security_credentials::private_key_path, and database::security::security_credentials::username.
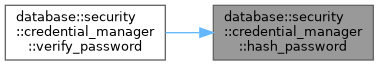
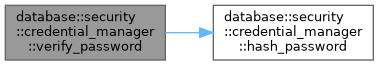
◆ hash_password()
| std::string database::security::credential_manager::hash_password | ( | const std::string & | password | ) | const |
Definition at line 175 of file secure_connection.cpp.
References database::security::password.
Referenced by verify_password().
◆ remove_credentials()
| bool database::security::credential_manager::remove_credentials | ( | const std::string & | connection_id | ) |
Definition at line 86 of file secure_connection.cpp.
References credentials_mutex_, and encrypted_credentials_.
◆ rotate_encryption_keys()
| bool database::security::credential_manager::rotate_encryption_keys | ( | ) |
Definition at line 98 of file secure_connection.cpp.
References credentials_mutex_, decrypt_data(), encrypt_data(), encrypted_credentials_, and master_key_.
◆ set_master_key()
| void database::security::credential_manager::set_master_key | ( | const std::string & | key | ) |
Definition at line 92 of file secure_connection.cpp.
References credentials_mutex_, and master_key_.
◆ store_credentials()
| bool database::security::credential_manager::store_credentials | ( | const std::string & | connection_id, |
| const security_credentials & | credentials ) |
Definition at line 30 of file secure_connection.cpp.
References database::security::security_credentials::auth_method, database::security::security_credentials::ca_cert_path, database::security::security_credentials::certificate_path, credentials_mutex_, encrypt_data(), encrypted_credentials_, database::security::security_credentials::encryption, database::security::security_credentials::password_hash, database::security::security_credentials::private_key_path, and database::security::security_credentials::username.
◆ verify_password()
| bool database::security::credential_manager::verify_password | ( | const std::string & | password, |
| const std::string & | hash ) const |
Definition at line 228 of file secure_connection.cpp.
References hash_password(), and database::security::password.
Member Data Documentation
◆ credentials_mutex_
|
mutableprivate |
Definition at line 124 of file secure_connection.h.
Referenced by get_credentials(), remove_credentials(), rotate_encryption_keys(), set_master_key(), and store_credentials().
◆ encrypted_credentials_
|
private |
Definition at line 125 of file secure_connection.h.
Referenced by get_credentials(), remove_credentials(), rotate_encryption_keys(), and store_credentials().
◆ master_key_
|
private |
Definition at line 126 of file secure_connection.h.
Referenced by decrypt_data(), encrypt_data(), rotate_encryption_keys(), and set_master_key().
The documentation for this class was generated from the following files:
- database/security/secure_connection.h
- database/security/secure_connection.cpp